Red Hat announced on Tuesday the general availability of a malware detection service for Red Hat Enterprise Linux (RHEL) systems.
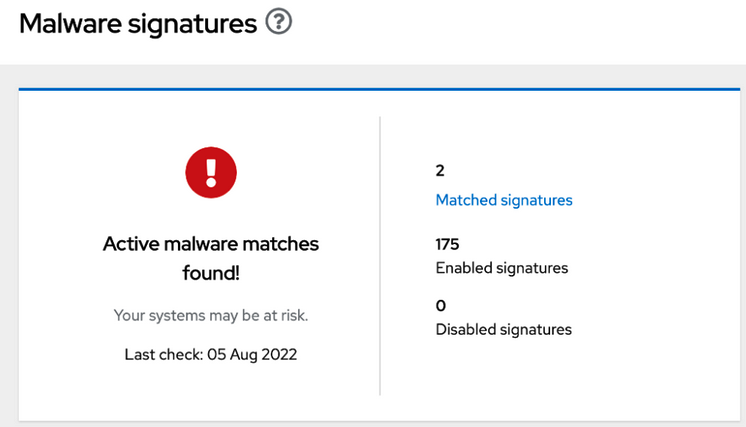
The Insights service, created in partnership with IBM X-Force, scans RHEL systems for malware using a database of more than 180 signatures associated with known Linux malware. Users can obtain aggregated results for all their systems or results for individual system scans.
RHEL 8 and 9 hosts are supported. Scans can be run manually, but they can also be scheduled or automated.
Red Hat told customers that scans will likely result in no detections in most cases. When malware is detected on a system, the user is provided information on the type of threat and a link to an IBM X-Force analysis report for more details.
A getting started guide for the malware detection service is available for RHEL customers.
While Linux malware is not as widespread as Windows malware, Linux users should not ignore the threat posed by malware. New Linux malware families continue to emerge and they appear to be increasingly sophisticated. Examples of malware discovered in the past year include Symbiote, Shikitega, Bvp47 and Lightning Framework.
Related: How Linux Became the New Bullseye for Bad Guys
Related: The Drovorub Mystery: Malware NSA Warned About Can’t Be Found
Related: CISA Tells Organizations to Patch Linux Kernel Vulnerability Exploited by Malware















