A serious vulnerability affecting the eCos SDK made by Taiwanese semiconductor company Realtek could expose the networking devices of many vendors to remote attacks.
The security hole, tracked as CVE-2022-27255 and rated ‘high severity’, has been described as a stack-based buffer overflow that can allow a remote attacker to cause a crash or achieve arbitrary code execution on devices that use the SDK. An attack can be carried out through the WAN interface using specially crafted SIP packets.
The Realtek eCos SDK is provided to companies that manufacture routers, access points and repeaters powered by RTL819x family SoCs. The SDK implements the base functionalities of the router, including the web administration interface and the networking stack. Vendors can build on top of this SDK to add custom functionality and their branding to the device.
Realtek informed customers about the eCos SDK vulnerability in March, when it announced the availability of a patch. However, it’s up to the OEMs using the SDK to ensure that the patch is distributed to end-user devices.
Researchers at Argentina-based cybersecurity firm Faraday Security have been credited by Realtek for discovering the vulnerability. Faraday researcher Octavio Gianatiempo, who is detailing the findings on Friday at the DEF CON conference in Las Vegas, shared some information with SecurityWeek ahead of the event.
The researcher said the vulnerability can be exploited remotely — directly from the internet — to hack affected routers running with default settings. No user interaction is required for successful exploitation.
“The vulnerable code is part of the networking stack — if the device is connected to the internet, an attacker only needs to send a packet to take control of the device,” he explained.
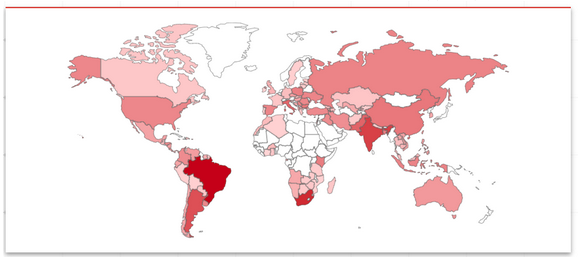
Gianatiempo said they have identified roughly 20 vendors that use the vulnerable SDK for their products, including Tenda, Nexxt, Intelbras, and D-Link. However, there could be other impacted vendors that they have yet to identify.
“The process of identifying affected OEM products is daunting due to the lack of visibility of their supply chain,” Gianatiempo noted.
While there is no indication that the flaw has been exploited in the wild, there could be a significant number of devices that are exposed to attacks due to this vulnerability, so it may be tempting for malicious actors.
Faraday has conducted a Shodan search and identified more than 60,000 vulnerable routers with their administration panel exposed. In addition, Mercadolibre, the largest ecommerce site in Latin America, has sold 130,000 devices affected by the vulnerability, according to a sales counter displayed on product pages.
“The admin panel is not enabled by default, so the total number of exposed devices should be greater,” Gianatiempo explained. “Remote identification of affected routers would require triggering the vulnerability, which is outside our research scope.”
Threat actors have been known to target Realtek SDK vulnerabilities in their attacks. Last year, researchers spotted exploitation of a flaw just days after its disclosure.
Related: Devices From Many Vendors Can Be Hacked Remotely Due to Flaws in Realtek SDK
Related: Vulnerabilities in Realtek Wi-Fi Module Expose Many Devices to Remote Attacks














