Authorities in California have confirmed that a cybersecurity incident involving the Department of Finance is being investigated after a cybercrime group claimed to have stolen tens of gigabytes of files from its systems.
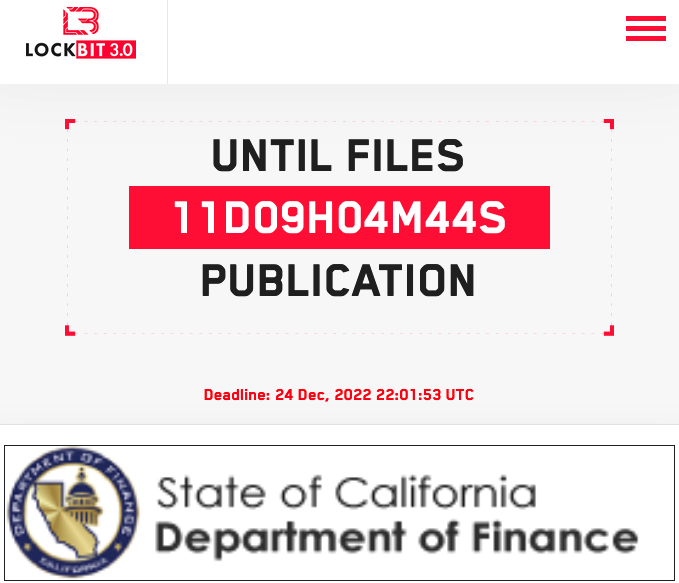
The notorious LockBit ransomware group listed the California Department of Finance on its Tor-based leak website on Monday, threatening to publish 76Gb of stolen information unless a ransom is paid by December 24.
The ransomware gang claims to have obtained “databases, confidential data, financial documents, certification, court and sexual proceedings in court, IT documents and more.”
The hackers published several screenshots representing financial information, a directory structure, a contract and other documents to prove their claims. The directory structure screenshot appears to demonstrate the claim that 76 Gb of data have been stolen.
It’s unclear if the hackers also encrypted data on California Department of Finance systems.
In a statement published on Monday, the California Governor’s Office of Emergency Services said the California Cybersecurity Integration Center (Cal-CSIC) is actively responding to an incident involving the Department of Finance.
No technical information has been shared due to the ongoing investigation, but authorities are confident that no state funds have been compromised.
LockBit has been around since 2019, and the LockBit 2.0 ransomware-as-a-service operation emerged in June 2021. LockBit 3.0 was announced one year later. LockBit has been one of the most active ransomware operations, accounting for a significant percentage of the ransomware attacks launched in 2022.
The hackers this year claimed to have targeted government organizations, including France’s Ministry of Justice, and major companies such as German car parts giant Continental.
Last month, a 33-year-old Russian and Canadian national was arrested in Canada over his role in LockBit ransomware attacks against critical infrastructure and major industrial groups worldwide. While authorities described the suspect as an operator, he is likely an affiliate — affiliates conduct attacks using malware and infrastructure provided by operators — and his arrest might not impact the LockBit operation too much.
Related: Thales Denies Getting Hacked as Ransomware Gang Releases Gigabytes of Data
Related: LockBit Ransomware Site Hit by DDoS Attack as Hackers Start Leaking Entrust Data
Related: French Hospital Diverts Patients Following Cyberattack















