Many devices made by Microsoft, Lenovo, Samsung and likely others are affected by potentially serious UEFI firmware vulnerabilities in Qualcomm Snapdragon chips.
Qualcomm announced this week the availability of patches for a dozen vulnerabilities, including five connectivity- and boot-related issues discovered by researchers at firmware security company Binarly.
Alex Matrosov, founder and CEO of Binarly, told SecurityWeek that they discovered a total of nine vulnerabilities while analyzing the firmware for Lenovo Thinkpad X13s laptops powered by the Qualcomm Snapdragon system-on-a-chip (SoC).
Further analysis revealed that while some of the nine flaws are specific to Lenovo devices, five of them impact Qualcomm reference code, which means the vulnerabilities are also present in laptops and other devices using Snapdragon chips.
The Snapdragon CPU uses the Arm architecture and Matrosov said this is the first such disclosure of UEFI firmware vulnerabilities related to the Arm device ecosystem.
According to Binarly, the Qualcomm vulnerabilities have been confirmed to impact — in addition to Lenovo devices — Arm-based Microsoft Surface and the Windows Dev Kit 2023 (Project Volterra) computers, as well as Samsung products.
“Based on Qualcomm’s advisory, the number of affected chipsets is massive,” Matrosov said via email.
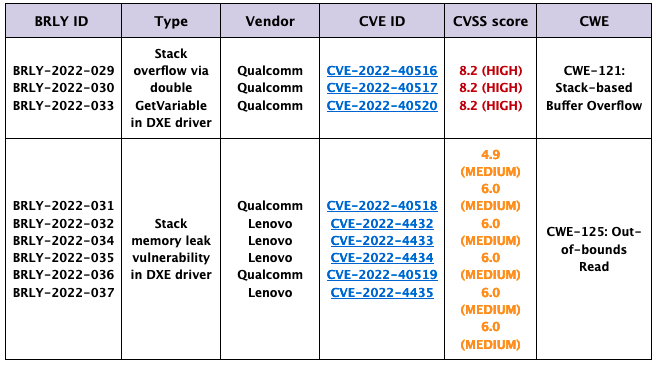
Two types of vulnerabilities were discovered — stack-based buffer overflows and out-of-bounds read issues — both related to the DXE driver. They can be exploited by local attackers with elevated privileges, according to Lenovo’s advisory.
Matrosov explained that three of the vulnerabilities can lead to arbitrary code execution and they have been assigned a ‘high severity’ rating. These flaws can be exploited for a Secure Boot bypass, and they “enable an attacker to gain persistence on a device by gaining sufficient privileges to write to the file system, thus allowing an attacker to cross an extra security boundary to simplify attacks on TrustZone.”
The remaining security holes have been rated ‘medium severity’ and they can lead to information disclosure.
Qualcomm said patches for the vulnerabilities found by Binarly were made available to customers in November 2022, and the company has encouraged affected end users to apply security updates when they become available from device makers.
Binarly plans on disclosing technical details in a blog post scheduled for January 9.
Related: New Firmware Vulnerabilities Affecting Millions of Devices Allow Persistent Access
Related: 16 Vulnerabilities Found in Firmware of HP Enterprise Devices
Related: Lenovo Patches UEFI Code Execution Vulnerability Affecting Many Laptops














