Swiss-based encrypted email services provider ProtonMail announced on Tuesday the launch of a new tool designed to help users securely manage their contacts.
According to the vendor, the new ProtonMail contacts manager has been in development for more than a year and it adds powerful functionality for managing the address book.
What makes ProtonMail Contacts highly secure is the fact that it uses zero-access encryption. This means contact information is encrypted and it can only be decrypted by the user – not even ProtonMail can access the data.
The company says the new encrypted contacts manager is ideal for journalists and other individuals for whom it’s critical that contact information is protected.
ProtonMail noted that the new feature secures phone numbers, physical addresses and other information added by the user, but it does not use zero-access encryption for email addresses as it would break email filtering functionality and it wouldn’t represent a significant privacy improvement considering that the service needs to know the recipient’s email address in order to deliver messages.
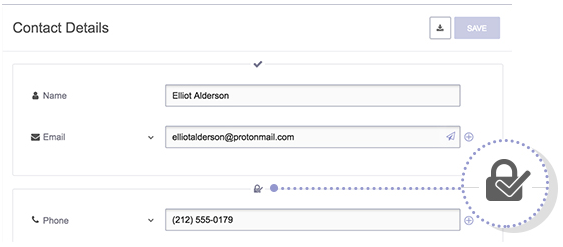
On the other hand, the new ProtonMail Contacts tool does provide some protection for email addresses by using digital signatures to verify their integrity. The digital signatures mechanism, which provides a cryptographic guarantee that contact data hasn’t been tampered with, covers all the information stored in the address book, not only email addresses. If the application detects an invalid signature, it displays an error message to alert the user.
“This is a big security benefit for many reasons,” ProtonMail said in a blog post. “For example, if an attacker wanted to intercept the communications between you and a sensitive contact, one way to do it could be to secretly change the email address or phone number you have saved for that contact, such as changing john.smith(at)protonmail.com to john.snnith(at)protonmail.com, which might escape your notice.”
The new contacts manager relies on new private and public key pairs for each account. The private key is generated based on the user’s password and it’s stored on the client side, preventing ProtonMail from gaining access to the encryption key. The same key pair is used both for encrypting contact information and digital signing.
The new contacts manager is currently only available for the web version of ProtonMail, but it will soon be added to the iOS and Android apps as well. Future versions of the tool will also allow users to store keys created for sending PGP-encrypted messages, ProtonMail said.
The source code for ProtonMail’s web client, including the contacts manager, is available on GitHub.
Related: ProtonMail Suspects State-Sponsored DDoS Attack
Related: Powerful DDoS Attack Cripples ProtonMail Service For Days















