While the number of identified vulnerabilities has increased significantly over the past years, the percentage of flaws that are exploitable or have actually been exploited has been dropping, according to vulnerability management company Kenna Security.
The number of vulnerabilities that received a CVE identifier in 2011 was roughly 4,100, but the number has exceeded 10,000 every year since 2016 — there were 14,000 in 2017, 16,000 in 2018 and 12,000 in 2019. The number of CVEs assigned so far this year has exceeded 17,000.
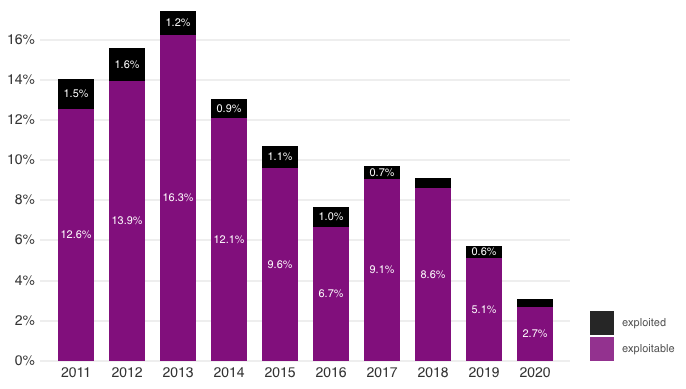
Kenna Security has conducted an analysis of more than 100,000 vulnerabilities disclosed since 2011 and noticed that the number of exploitable and exploited flaws has been on a downwards trend over the past years.
In 2017, 9.1% of vulnerabilities were exploitable and 0.7% of them were actually exploited. In 2020, only 2.7% of security bugs appear to be exploitable and only roughly 0.4% of them have actually been exploited in attacks.
According to Kenna, in terms of severity, 8.6% of the critical vulnerabilities disclosed this year are exploitable and 2.1% have been exploited in attacks. One percent and 0.002% of the high-severity flaws are exploitable and have been exploited, respectively.
“Although the known universe of vulnerabilities is exploding, an increasingly small number of those vulnerabilities result in actual breaches. Focusing your remediation efforts on high-impact mitigations has never been more important,” Kenna Security told organizations.
While a majority of high- and critical-severity vulnerabilities still impact applications, the company says OS-level flaws account for an increasing proportion of serious flaws.
*updated the number of CVEs assigned in the past years
Related: Microsoft Explains How It Processes Vulnerability Reports
Related: IoT Security Foundation Launches Vulnerability Reporting Platform
Related: Microsoft Introduces Device Vulnerability Report in Defender for Endpoint
Related: NSA Lists 25 Vulnerabilities Currently Targeted by Chinese State-Sponsored Hackers














