The Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) last week published its annual vulnerability coordination report for the fiscal year 2015. The report provides details on the number and types of security holes disclosed to the agency last year.
ICS-CERT published 197 advisories and 16 alerts in 2015, which cover a total of 427 vulnerabilities. This is a considerable increase from the previous year when the organization was only informed of 245 issues.
There is also an increase in the percentage of vulnerabilities coordinated with ICS-CERT – only roughly 7 percent of these flaws were disclosed without allowing the vendor to release a patch, compared to nearly 20 percent in 2014.
The researcher who reported the highest number of vulnerabilities to ICS-CERT in 2015 is Maxim Rupp, who has identified weaknesses in products from Moxa, Accuenergy, ICONICS, Tollgrade, American Auto-Matrix and others. The list of experts who reported flaws in 2015 also includes Ivan Sanchez, Alexander Bolshev, Aditya K Sood, Karn Ganeshen and Martin Jartelius.
According to ICS-CERT, 43 percent of the security holes reported last year have been rated high severity, a considerable drop compared to the previous year, when more than 70 percent of flaws were classified as high severity. The average CVSS scores have gradually decreased over the past years, from 8.55 in 2010 to 6.85 in 2015.
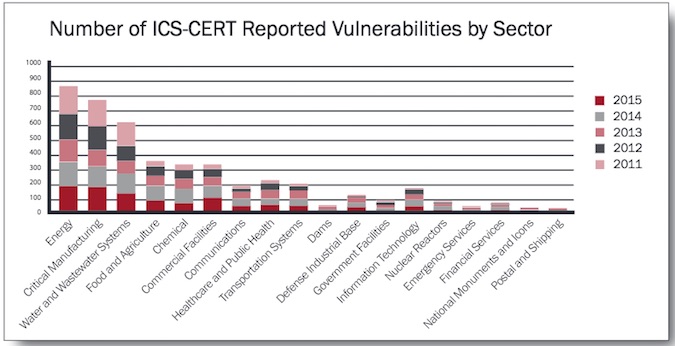
As for the most affected industries, the energy sector tops the chart, with more than 800 vulnerabilities reported since 2011, followed by critical manufacturing, with over 700 flaws. The water and wastewater systems sector was also impacted by over 600 bugs.
The most common types of vulnerabilities discovered in FY 2015 were related to permissions, privileges and access control (27%), improper input validation (25%), credentials management (19%), improper control of a resource (12%), cryptography (11%) and poor quality code (6%).
Related: Learn More at the ICS Cyber Security Conference
Related: One-Third of ICS Flaws Are Zero-Days When Disclosed
Related: U.S. Has Most Internet Connected Industrial Control Systems
















