Still under development, a newly discovered information stealer is successfully targeting Internet browsers and cryptocurrency wallet applications, and most victims are apparently located in the United States.
The fairly new malware, which has been dubbed Oski Stealer, is being advertised on underground cyber-forums, including several Russian forums, security researcher Aditya K Sood explained in a report shared with SecurityWeek.
The malware is designed to gather sensitive information such as credentials, credit card numbers, wallet accounts, and more, and has already managed to steal over 50,000 passwords.
Oski Stealer is being distributed via drive-by downloads, phishing attacks, and other standard infection methods, and acts as a native piece of software that can be installed on various systems. The malware targets both x86 and x64 versions of Windows 7, 8, 8.1 and 10, and can be installed without admin rights.
Once it has infected a machine, the stealer attempts to retrieve sensitive information from both Chromium- and Firefox-based browsers (Chromium, Chrome, Opera, Comodo Dragon, Yandex, Vivaldi, Firefox, Pale Moon, Cyberfox, BlackHawk, K-Meleon, etc), as well as from Filezilla and cryptocurrency wallets (Bitcoin Core, Ethereum, ElectrumLTC, Monero, Electrum, Dash, Litecoin, ZCash, and many others).
The malware is designed to extract credentials from registry, from the browser SQLite database, and by performing man-in-the-browser (MitB) attacks by hooking the browser processes using DLL injection, as well as to extract stored session cookies, including wallets.
Data exfiltration is performed via HTTP POST requests — it is sent in compressed format, either a zipped file or using a custom encryption for the HTTP POST body. Files containing data for exfiltration are stored in a folder in the ProgramData directory.
While analyzing the threat, the security researcher was able to access its command and control (C&C) server, which provided information on ongoing activity. The C&C domain, which was created last month and updated recently, is hosted on a server in Russia and can be accessed from any device connected to the Internet, the researcher told SecurityWeek.
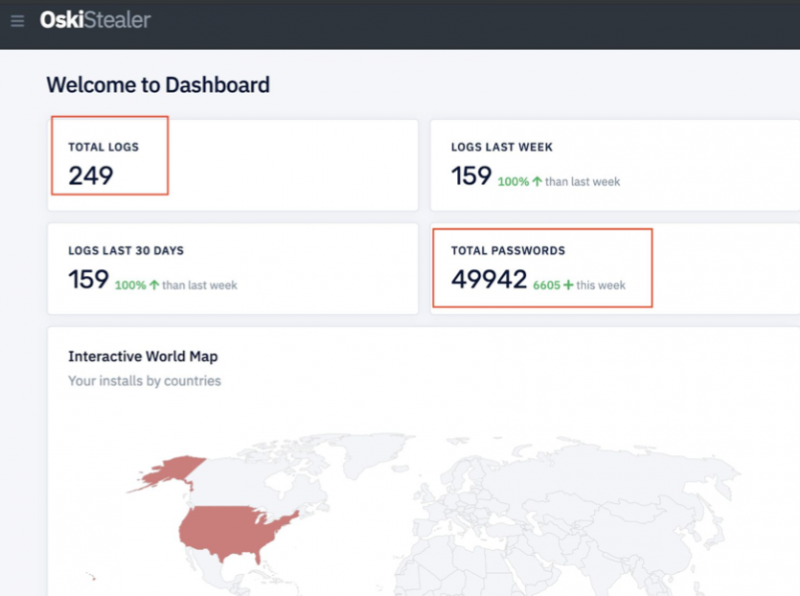
Initially, the dashboard served when accessing the C&C would show a total number of 88 logs and 43,336 compromised password. Within 10 hours, the number of logs increased to 249, while the number of passwords went up to 49,942, the researcher notes.
Soon after, the researcher accessed the C&C again, only to find that the number of logs had increased to 268, while that of stolen passwords hit 50,726.
The malware currently appears to focus on the United States and most of the data was stolen from Chromium browsers (over 97%). Moreover, the threat has mostly stolen Google account passwords.
“Our research revealed that Oski stealer is in early stages but it is a very effective stealer. Oski stealer has been deployed successfully in the wild and already extracting sensitive data such as credentials from the browsers. The deployment that we analyzed was targeting specifically the North America region,” Sood notes.
Related: ‘Masad Stealer’ Uses Telegram to Exfiltrate Data
Related: Baldr Malware: A Short-Lived Star or Info Stealer That Will Return?















