The Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the National Security Agency (NSA) have published a list of the top vulnerabilities that Chinese state-sponsored cyberspies have been exploiting in attacks since 2020.
In a joint advisory, the three US agencies warn of continuous abuse of vulnerable appliances by Chinese advanced persistent threat (APT) actors in attacks targeting the US and allied nations, mainly with the purpose of stealing intellectual property and maintaining access to compromised networks.
The Chinese APTs, the US agencies say, represent “one of the largest and most dynamic threats to U.S. government and civilian networks” due to the continuous targeting of government and critical infrastructure with new and adaptive techniques.
However, Chinese hackers continue to exploit known vulnerabilities when targeting networks of interest, and the US agencies urge organizations in all sectors to apply available patches in a timely manner to prevent potential compromise.
“NSA, CISA, and FBI assess PRC state-sponsored cyber actors have actively targeted U.S. and allied networks as well as software and hardware companies to steal intellectual property and develop access into sensitive networks,” the three agencies note.
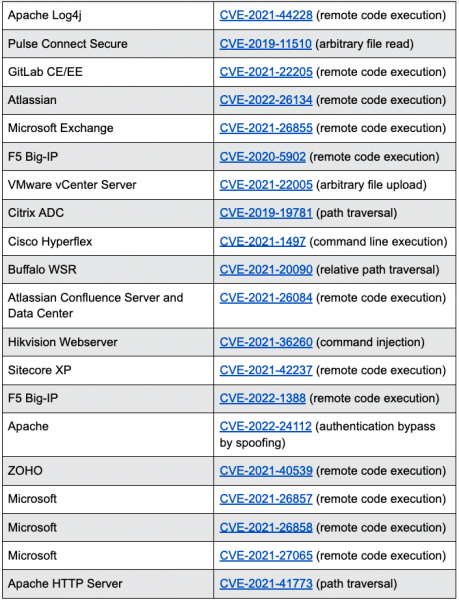
The 20 top vulnerabilities that Chinese hackers have been targeting in attacks over the past two years impact popular software from Microsoft, Apache, VMware, Cisco, Atlassian, and others.
“Many of the CVEs indicated […] allow the actors to surreptitiously gain unauthorized access into sensitive networks, after which they seek to establish persistence and move laterally to other internally connected networks,” CISA, the FBI, and the NSA note.
The three agencies also point out that the state-sponsored actors use virtual private networks (VPNs) to hide their activities and that initial access is gained by targeting web-facing applications.
To mitigate the risk posed by these Chinese hackers, organizations are advised to always keep their systems updated and patched, to employ multi-factor authentication (MFA), to block or remove unused protocols, to adopt a zero trust model, to enable logging on all internet-facing assets, and to replace end-of-life devices.
Related: US Details Chinese Attacks Against Telecoms Providers
Related: CISA Again Warns U.S. Organizations of Potential Russian Cyberattacks
Related: Chinese Hackers Using Publicly Available Resources in Attacks on U.S. Government














