Industrial, engineering and other types of organizations from around the world have been targeted in a profit-driven campaign dubbed by Kaspersky Lab “Operation Ghoul.”
The threat group, whose activities have been traced back to March 2015, has been trying to make money by hijacking bank accounts and stealing intellectual property that they can sell to interested parties. The cybercrime gang has targeted more than 130 organizations in over 30 countries.
According to the security firm, Operation Ghoul attacks start with a malicious email coming from a spoofed address that appears to belong to a bank. The emails typically carry a file attachment or contain links that point to phishing websites. The fake messages are mostly sent to executives, managers and other employees that could have access to valuable information.
The piece of malware delivered by the attackers is HawkEye, a commercial spyware capable of collecting keystrokes, screenshots, clipboard data, FTP credentials, app license information, and account data from browsers, messaging apps and email clients.
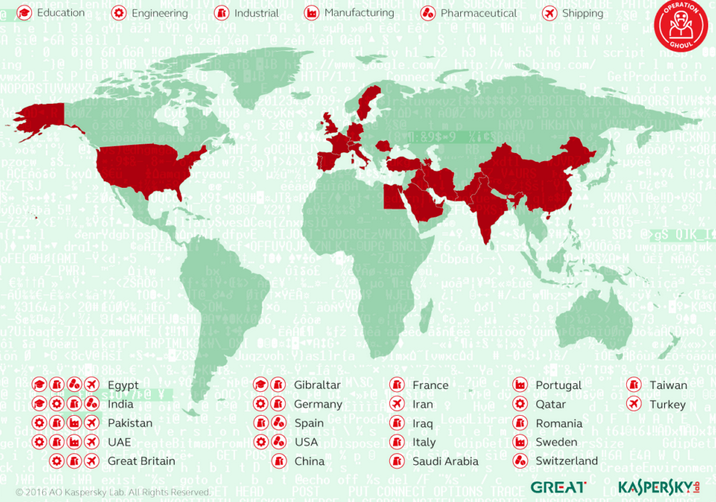
Kaspersky Lab has identified victims in Spain, Pakistan, UAE, India, Egypt, UK, Germany, Saudi Arabia, Portugal, Qatar and other countries. The targeted organizations are typically small and medium-sized businesses (SMBs) with 30 to 300 employees.
Roughly half of the Operation Ghoul victims are in the industrial sector, including petrochemical, naval, military, aerospace, solar energy and heavy machinery firms. The threat group has also targeted companies in the engineering, shipping, pharmaceutical, manufacturing, trade, education, IT and technology, and tourism sectors.
The latest attack waves, which Kaspersky spotted in June, focused on the Middle East, particularly the United Arab Emirates.
“In ancient Folklore, the Ghoul is an evil spirit associated with consuming human flesh and hunting kids, originally a Mesopotamian demon, and today, the term is sometimes used to describe a greedy or materialistic individual,” said Kaspersky researcher Mohammad Amin Hasbini.
“This is quite a precise description of the group behind Operation Ghoul. Their main motivation is financial gain resulting either from sales of stolen intellectual property and business intelligence, or from attacks on their victim’s banking accounts. Unlike state-sponsored actors, which choose targets carefully, this group and similar groups might attack any company. Even though they use rather simple malicious tools, they are very effective in their attacks. Thus companies that are not prepared to spot the attacks, will sadly suffer,” the expert added.
Attribution is often difficult, but even more so in this case as the attackers have been using off-the-shelf malware such as HawkEye. The HawkEye spyware has been used to target entities all around the world in various types of campaigns.
Related Reading: MONSOON Cyber-Espionage Campaign Linked to Patchwork APT
Related Reading: “Strider” Espionage Group Targets China, Russia, Europe
Related Reading: Cyber Espionage Targets Interests in South China Sea















