A new variant of the Buer malware loader has been detected, written in Rust. The original version is written in C. Rust is efficient, easy-to-use, and an increasingly popular programming language – Microsoft uses it, and joined the Rust Foundation in February 2021.
Researchers at Proofpoint identified the new variant in early April 2021, and named it RustyBuer. Like Buer, it works as a downloader to distribute other malware to compromised systems. The most likely reason for the development of a Rust variant is to evade anti-malware detections that are based on features of the malware written in C.
In the associated campaigns detected by Proofpoint, the malware is distributed by DHL-themed phishing emails and is used to deliver malicious Word or Excel documents.
In one example, an Excel attachment had RustyBuer embedded as a macro. The document showed multiple security firm logos, presumably in an attempt to add legitimacy. The macro leveraged an Application Bypass (Windows Shell DLL via LOLBAS) to evade detection from endpoint security mechanisms.
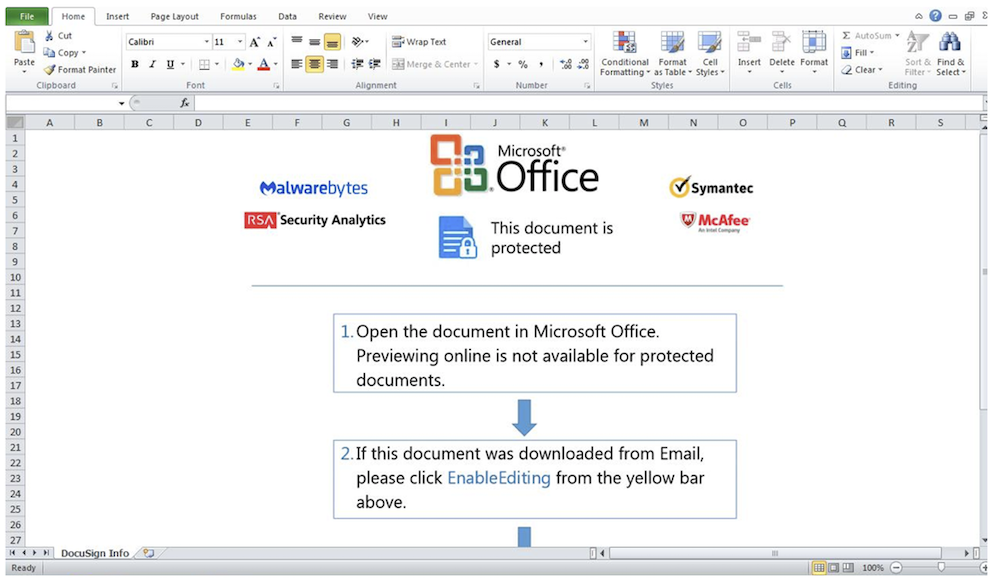
Figure 1. RustyBuer malicious Excel attachment
If the document is viewed, RustyBuer is dropped and persistence established by using a LNK file that runs at start-up. The Proofpoint researchers have seen the loader deliver Cobalt Strike Beacon as a second-stage payload, but not all samples contained a second-stage payload. In the latter case, say the researchers, “These threat actors may be attempting to establish initial access in victim environments to then sell their access to other threat actors in underground marketplaces.”
RustyBuer attempts to avoid analysis by checking for virtual machines. It also has a limited geographical check to avoid running in specific countries – mainly, it seems, in countries appearing to be a part of the Commonwealth of Independent States (CIS). This could be an indication that the developers have some association with Russia where the authorities appear to be fairly relaxed about hackers that do not attack targets within Russia.
Communication with C2 servers is almost identical to those used in the latest version of the C language variant. Functions are handled via HTTP(S) POST requests. The initial POST request will be sent with POST data delimitated by the “&” and “=” characters. The request parameters are encrypted and can be decrypted by Base64 decoding, Hex decoding, and RC4 decryption. It contains basic information of the compromised computer.
The response beacon can be similarly decoded. As with the original Buer variant, it contains various options on how to download and execute a payload. Combining Buer/RustyBuer’s access-as-a-service with malware-as-a-service means that criminals with little technical expertise can now deliver sophisticated malware – including ransomware – to targets of their choice.
Commenting on the Proofpoint findings, CTO and cofounder of Blue Hexagon Saumitra Das, said, “Rust-based malware has been gaining popularity over the last few years. It is becoming more common as attackers try to evade improving detection systems.” He added, “There are already open-source implementations of sample malware Ransomware,” giving the example of Rust-Ransomware on GitHub.
Proofpoint suggests that the emergence of RustyBuer demonstrates that the threat actors are continuing to evolve their malware in an attempt to evade detection, and that consequently “the attack chain may be more effective in obtaining access and persistence.” It adds, “RustyBuer and the original Buer loader have been observed as a first-stage loader for additional payloads including Cobalt Strike and multiple ransomware strains, as well as possibly providing victim access to other threat actors in the underground marketplace.
The key takeaway for defenders is that old malware compiled in a new or different language will effectively be undetectable zero-day malware to signature-based detection systems until such time as the vendors find and analyze the malware and add a new signature to their detection engine.
Proofpoint last week agreed to be acquired by private equity firm Thoma Bravo in an all-cash transaction valued at approximately $12.3 billion.
















