Security researcher Patrick Wardle has been looking at ways to generically detect ransomware attacks on Mac OS X systems and he has developed a tool that appears to be capable of accomplishing the task.
Wardle, director of research at Synack, is well-known in the industry for bypassing Apple’s Gatekeeper security feature. The expert has developed several OS X security tools in the past and on Wednesday he announced the release of a new one.
The tool, named “RansomWhere?”, is designed to detect and block any type of file-encrypting ransomware on OS X by continually monitoring the file system for the creation of encrypted files by suspicious processes.
There have been several reports over the past years about ransomware targeting Mac OS X users. Early threats were designed to simply lock users’ browsers and could be easily removed, but newer ransomware, such as KeRanger, pose a more serious threat.
KeRanger, which is considered the first fully functional ransomware targeting OS X, attempts to encrypt 300 different file types on infected systems. The malware bypassed Gatekeeper because it was delivered via a compromised installer that was signed with a valid app development certificate issued by Apple.
After analyzing various pieces of ransomware, Wardle came up with the idea that such threats can be generically identified by monitoring file I/O events and detecting the rapid creation of encrypted files by untrusted processes. For this, he needed to find ways to monitor file I/O events, determine if a file is encrypted, and identify untrusted processes.
There are several tools and methods that can be used to monitor file I/O events on OS X, including dtrace, fs_usage, OpenBSM, and fsevents. The expert chose the direct use of fsevents, which he also leveraged in another one of his tools called BlockBlock.
In order to determine if a file is encrypted, Wardle used available documentation on differentiating encryption from compression based on mathematical calculations.
The problem is that even legitimate applications can create encrypted files (e.g. password managers). In order to avoid the classification of such apps as ransomware, the tool developed by Wardle considers all processes signed by Apple and ones already installed on the system when the tool is first run inherently trusted.
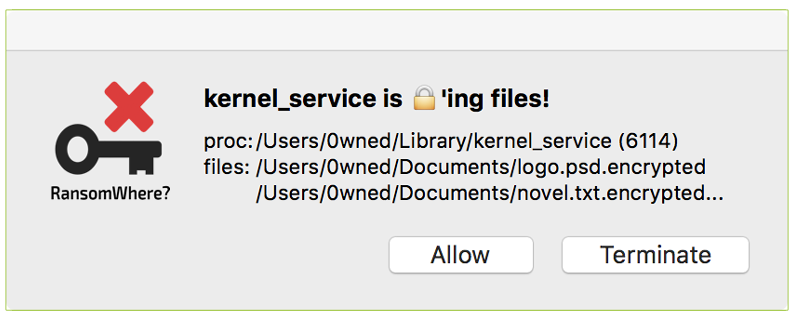
RansomWhere? is installed as a launch daemon with the “RunAtLoad” key set to “true” so that it’s automatically executed when the system boots. It then enumerates all installed applications to create a baseline, classifies running processes, and starts monitoring file I/O events. When an untrusted process is found rapidly creating encrypted files, the process in question is suspended and the user is alerted. RansomWhere? users can allow the process to continue or terminate it.
Wardle successfully tested the tool against Gopher, a proof-of-concept ransomware created last year by OS X security expert Pedro Vilaca, and KeRanger. The researcher pointed out that while the tool can generically detect and block OS X ransomware, version 1.0.0 does have several limitations and a piece of ransomware specifically designed to bypass it would likely succeed.
The limitations include the fact that RansomWhere? does allow some files to get encrypted before blocking the ransomware, it currently only monitors the user’s home folders, and it ignores potential threats that abuse a signed Apple binary. Despite the limitations, Wardle believes this approach could be highly efficient for detecting OS X ransomware.
The researcher told SecurityWeek that the same principle could also work on Windows and Linux operating systems. When he came up with the idea for RansomWhere?, Wardle found discussions about CryptoMonitor, an apparently similar Windows anti-ransomware tool that Malwarebytes has started integrating in its products.
RansomWhere? is currently closed-source, but Wardle says he might release it as open source in the future. In the meantime, he published a blog post containing numerous code snippets and a detailed technical description of how the tool works.










