Threat intelligence firm Anomali on Monday announced the launch of Lens, a new tool designed to make it easier for organizations to find and use threat data from a wide range of sources.
Anomali Lens is part of the company’s Altitude solution, which also includes its flagship threat intelligence platform ThreatStream and Match, a breach detection platform that matches external threat intelligence to internal events.
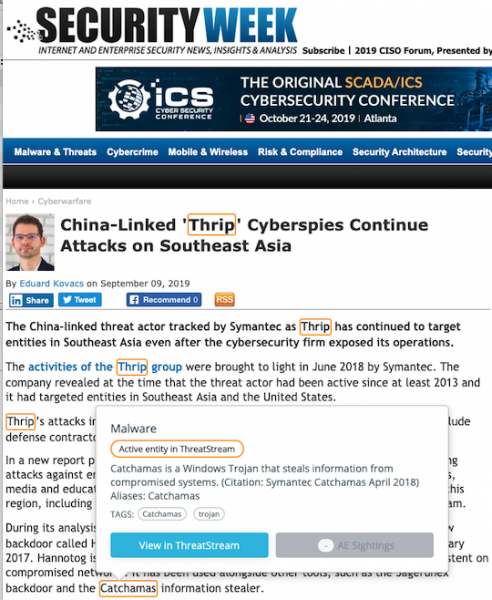
Lens provides users a web browser extension designed to highlight and collect relevant threat data on the web pages they visit, including news articles, blogs, security bulletins, logs, research papers, incident response reports, and social media.
Once a page is scanned, each data element — this can include threat actor names, malware, IP addresses and CVE identifiers — is highlighted using specific colors that indicate the extent to which a threat is known.
Users can then create a threat bulletin that contains the collected data or initiate an investigation. The data is also added to ThreatStream and matched with internal network events via the Match platform. This allows organizations to check if they have been impacted by the analyzed threat and helps them defend their environments against future attacks.
Anomali Lens makes it easy to import useful data from malware analysis websites such as VxCube in order to determine if a specific piece of malware impacts the customer’s environment — and if so, to what extent.
In the case of CVEs, it can show organizations if they are affected by actively exploited or high-risk software vulnerabilities that they may have previously ignored.
Anomali says the new tool, which is immediately available, can be highly useful to various types of users, including analysts, C-level executives — it makes it easier for them to understand if a threat impacts their organization — and even journalists.
The Anomali Lens browser extension is currently available for Chrome and Firefox, but the vendor told SecurityWeek that it’s working on rolling out native support for Windows and macOS in future releases.
The company also said it plans on adding support for mobile devices, and advanced methods for identifying attack techniques, such as URL injection and cross-site scripting (XSS).
Related: Threat Intelligence Tech Firm Anomali Raises $40 Million
Related: Multiple Chinese Groups Share the Same RTF Weaponizer













