Netflix has published tools and information to help defenders identify systems that could be leveraged by malicious actors for damaging application layer distributed denial-of-service (DDoS) attacks.
Akamai’s State of the Internet report for the first quarter of 2017 shows that application layer attacks accounted for less than one percent of DDoS attacks. However, security engineers at Netflix warn that they can pose a serious threat to organizations relying on a microservice architecture.
The microservices architecture is an increasingly popular method for developing software. In a microservices architecture, the application relies on multiple smaller and independent services that communicate with other services to serve a business goal.
The problem with this type of architecture, from a security standpoint, is that there may be a gateway API that sends out thousands of requests to middle tier and backend services from a single request.
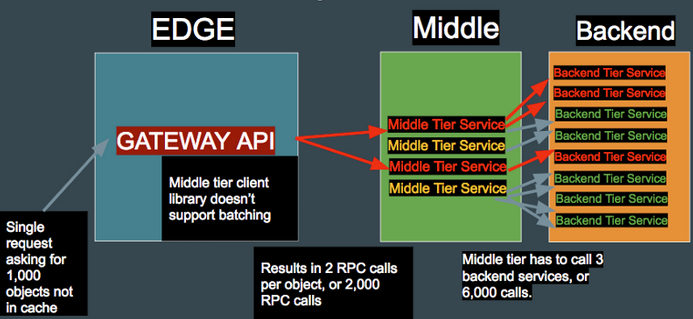
If an attacker can identify an API that fans out into a large number of requests to middle and backend services, they may be able to generate a DoS condition in middle tier services and cause an overall service outage, Netflix warned.
“All of this is made possible because the microservice architecture helps the attacker by massively amplifying the attack against internal systems. In summary, a single request in a microservices architecture may generate tens of thousands of complex middle tier and backend service calls,” said Netflix security engineers Scott Behrens and Bryan Payne, who had a talk on this topic last week at the DEF CON conference.
The security experts have provided instructions on how defenders can analyze their systems in order to identify potentially problematic APIs. Netflix has also released a couple of open source testing tools for application DDoS.
Repulsive Grizzly is a framework designed to make it easier for organizations to look for weak spots. It can be used in combination with Cloud Kraken, the second tool released as open source by Netflix, to conduct tests at a larger scale across multiple data centers and regions.
Netflix made available the source code of several internal tools in the past years, including for collecting intelligence, discovering cross-site scripting (XSS) flaws, and securing devices.
Related: Fake Netflix App Takes Control of Android Devices
Related: Netflix Login Generator Distributes Ransomware
Related: Cisco Releases Open Source Malware Signature Generator












