Mozilla announced on Thursday that it has expanded its bug bounty program with a new category that focuses on bypass methods for the exploit mitigations, security features and defense-in-depth measures in Firefox.
Mozilla says mitigation bypasses have until now been classified as low- or moderate-severity issues, but they are now eligible for a reward associated with a high-severity flaw as part of the new Exploit Mitigation Bug Bounty.
This means a bypass mitigation with privileged access can earn researchers up to $5,000 if they submit a high-quality report. However, if the mitigation is bypassed without privileged access — this typically involves chaining more than one weakness — researchers can receive a reward for the vulnerability itself and a 50 percent bonus for the mitigation bypass.
Mozilla says it still encourages researchers to test Firefox Nightly, the testing and development version of the browser, but vulnerabilities found in Nightly will only be eligible for a bounty if they’re not found internally by Mozilla within four days of the code change that introduces the flaw being posted to the primary repository.
Some have criticized Mozilla for expanding its bug bounty program shortly after it laid off some of its cybersecurity staff. However, the company told SecurityWeek that the recent layoffs did not impact the teams responsible for the security of the Firefox browser and Firefox services.
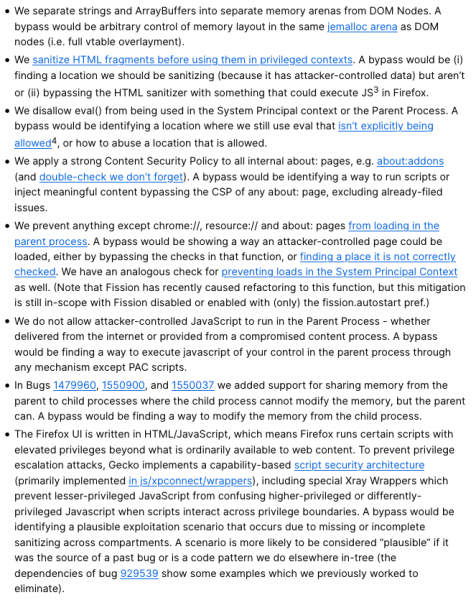
Mozilla has posted a list of the mitigations covered by the Exploit Mitigation Bug Bounty:
Related: Firefox, IE Vulnerabilities Exploited in Attacks on China, Japan
Related: Details Released for Recently Patched Code Execution Vulnerability in Firefox
Related: Cisco Discloses Details of Chrome, Firefox Vulnerabilities












