Log4Shell Attacks Can Be Launched by Luring Targets to Malicious Website
Customers of the MobileIron security and endpoint management product are being targeted in Log4Shell attacks, just as researchers identify new attack vectors and Cloudflare reports a surge in exploit activity.
Ivanti, which owns MobileIron, has informed customers that the MobileIron Core, Sentry and Core Connector products are affected by the recently disclosed Log4j vulnerability tracked as CVE-2021-44228, Log4Shell and LogJam. The vendor provided mitigations and warned that “the risk associated with CVE-2021-44228 is High because these products sit in the DMZ and are vulnerable to a RCE attack due to the CVE.”
The Log4Shell flaw has been exploited by both profit-driven cybercriminals and state-sponsored groups, including ones linked to China, Iran, North Korea and Turkey.
NCC Group’s researchers have seen attacks aimed at MobileIron users — the company had seen 5 instances in its customer base as of December 15. The attacks appear to rely on a Log4Shell payload aimed at MobileIron that was made public this week.
There are more than 4,600 MobileIron instances exposed to the internet, mainly in the United States and Germany.
Cloudflare reported that overall Log4Shell activity surged on December 16, with well over 100,000 attacks per minute at certain times — this includes both actual exploitation attempts and scanning for vulnerable systems.
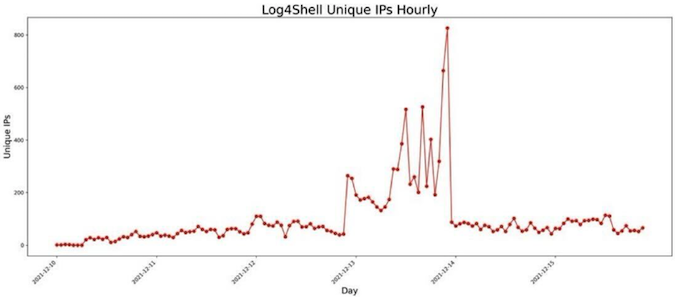
On the other hand, threat intelligence company GreyNoise reported seeing a drop in the number of unique IP addresses scanning for the Log4j vulnerability. The company has published a graph showing activity by both researchers and other actors.
New attack vectors and shifting focus to other protocols
Exploitation of the Log4Shell vulnerability involves sending a specially crafted request to the targeted system. The request generates a log using Log4j, which leverages the Java Naming and Directory Interface (JNDI) lookup feature to perform a request to an attacker-controlled server, from which a malicious payload is fetched and executed.
Log4j developers have disabled access to JNDI by default in response to the risk posed by this functionality.
In most cases, the vulnerability has been exploited using the Lightweight Directory Access Protocol (LDAP) service, but there are several other protocols that can be — and have been — abused as well.
Fastly has also seen a surge in attacks this week and noted that while attackers still mainly focus on LDAP, a significant percentage leverages Remote Method Invocation (RMI). Juniper Networks reported that attackers had started shifting focus from LDAP to RMI.
Another important finding comes from Blumira, whose researchers have found a way to exploit the Log4Shell vulnerability by getting the target to access a specially crafted website. For the time being, there is no evidence that this method has been used for malicious purposes.
“Previously, we understood that the impact of Log4j was limited to vulnerable servers,” Blumira explained. “This newly-discovered attack vector means that anyone with a vulnerable Log4j version on their machine or local private network can browse a website and potentially trigger the vulnerability.”
Related: Log4Shell Tools and Resources for Defenders – Continuously Updated
Related: Industry Reactions to Log4Shell Vulnerability (12/15/2021)
Related: Industrial Organizations Targeted in Log4Shell Attacks














