A serious vulnerability affecting the NetUSB kernel driver developed by Taiwan-based tech company KCodes exposes millions of routers to hack attacks, researchers have warned.
According to its website, KCodes is one of the leading developers and suppliers of USB over IP solutions. The company says over 20% of world’s networking devices include KCodes technology.
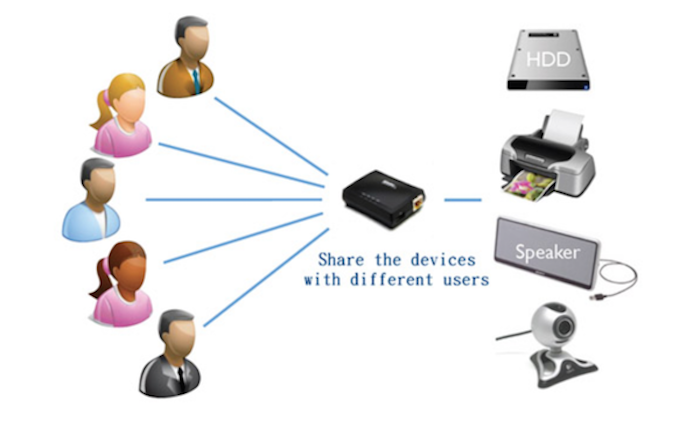
The NetUSB (USB over IP) kernel driver developed by the company is designed to allow users to connect over their network to USB devices plugged into a router, access point, or other Linux-based embedded system. Users can access speakers, printers, hard drives, webcams and other USB devices by connecting to a NetUSB server via the Windows or OS X client.
Researchers at SEC Consult discovered that the NetUSB driver is plagued by a kernel stack buffer overflow vulnerability (CVE-2015-3036) that can be exploited by an unauthenticated attacker to execute arbitrary code or cause a denial-of-service (DoS) condition. The flaw, caused by insufficient input validation, can be triggered by specifying a computer name that is longer than 64 characters when the client connects to the server.
KCodes’ NetUSB driver is integrated into products from several vendors, including Netgear, TP-Link, ZyXEL, and TRENDnet. The feature is advertised with various names, such as “print sharing,” “USB share port” and “ReadySHARE.”
SEC Consult has confirmed that the vulnerability affects the latest firmware versions for TP-Link TL-WDR4300 V1, TP-Link WR1043ND v2, and Netgear WNDR4500. Researchers also identified the NetUSB feature in tens of router models from D-Link, Netgear, TP-Link, TRENDnet, and ZyXEL.
Furthermore, a component of the driver makes references to a total of 26 vendors that have likely licensed the NetUSB technology. The list includes Allnet, Ambir Technology, AMIT, Asante, Atlantis, Corega, Digitus, EDIMAX, Encore Electronics, Engenius, Etop, Hardlink, Hawking, IOGEAR, LevelOne, Longshine, PCI, PROLiNK, Sitecom, Taifa, and Western Digital.
The vulnerability can be exploited by an attacker on the local network, but in some cases exploitation over the Internet might also be possible through TCP port 20005, the port used by the server for client connections.
“While NetUSB was not accessible from the internet on the devices we own, there is some indication that a few devices expose TCP port 20005 to the internet. We don’t know if this is due to user misconfiguration or the default setting within a specific device. Exposing NetUSB to the internet enables attackers to get access to USB devices of potential victims and this would actually count as another vulnerability,” SEC Consult wrote in a blog post.
SEC Consult informed KCodes of the existence of the vulnerability in February, but so far the vendor has failed to properly communicate the status of a patch.
The security firm told SecurityWeek that it hasn’t heard from KCodes since March 25, but it has learned that Netgear and TP-Link received patches for their firmware from the developer. Vendors can’t address the bug without the patch from KCodes, SEC Consult noted.
“To this day, only TP-LINK released fixes for the vulnerability and provided a release schedule for about 40 products. Sometimes NetUSB can be disabled via the web interface, but at least on NETGEAR devices this does not mitigate the vulnerability. NETGEAR told us, that there is no workaround available, the TCP port can’t be firewalled nor is there a way to disable the service on their devices,” SEC Consult said.
KCodes has not responded to SecurityWeek’s request for comment by the time of publication.
CERT/CC, which released an advisory for the vulnerability on Tuesday, has reached out to other potentially impacted vendors to determine if their products are affected. Other CERTs are also involved in vendor coordination.














