Microsoft warned on Thursday that a recently uncovered piece of malware designed to help cybercriminals steal information from infected systems is now actively distributed in the wild.
The malware has been named Anubis, but the tech giant has pointed out that it’s not related to the Android malware that has the same name.
The new threat targets Windows systems and it’s detected by Microsoft security solutions as PWS:MSIL/Anubis.G!MTB. The company says Anubis uses code forked from the information-stealing trojan called Loki, and it’s capable of harvesting system information, payment card details, credentials, and cryptocurrency wallets.
Microsoft says Anubis was first spotted being sold on cybercrime forums in June, but it’s now actively being distributed in the wild.
“Anubis is deployed in what appears to be limited, initial campaigns that have so far only used a handful of known download URLs and C2 servers,” the company explained.
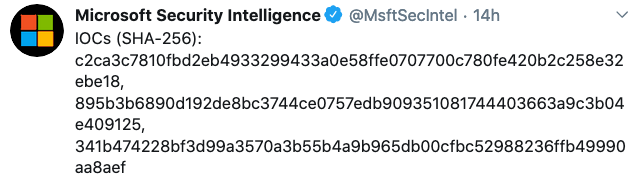
Microsoft says it will continue to monitor the info-stealer, but in the meantime it has shared some indicators of compromise (IoC), which can be used to detect the malware or to further analyze it.
Related: Enterprises in Americas, Europe Targeted With Valak Information Stealer
Related: Oski Stealer Targets Browser Data, Crypto Wallets in U.S.
Related: Baldr Malware: A Short-Lived Star or Info Stealer That Will Return?
Related: Emotet Resumes Activity After Five Months of Silence















