Microsoft on Thursday unveiled two new cloud-based security products and services — Microsoft Azure Sentinel and Microsoft Threat Experts — designed to make it easier for security teams to do their job.
The tech giant says security teams are often overwhelmed by threats and alerts. These alerts can turn out to be false positives, but by the time they figure it out, security staff may have already spent a significant amount of time investigating the potential threat.
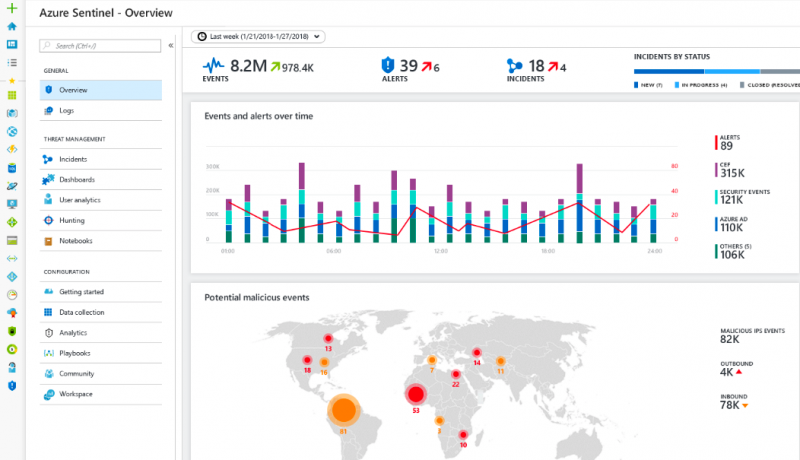
Microsoft Azure Sentinel aims to address this by providing a cloud-based security information and event management (SIEM) platform that leverages artificial intelligence to help identify and block threats while reducing the workload of security teams.
“With AI on your side it helps reduce noise drastically—we have seen an overall reduction of up to 90 percent in alert fatigue with early adopters. Because it’s built on Azure you can take advantage of nearly limitless cloud speed and scale and invest your time in security and not servers,” Microsoft said.
Available in preview from the Azure portal, Azure Sentinel can be integrated with security platforms and productivity tools from other vendors, including Check Point, Cisco, F5 Networks, Symantec, Palo Alto Networks and Fortinet. It also allows users to easily combine their Office 365 data with security data for analysis.
As for Microsoft Threat Experts, the company says it’s a new service within Windows Defender ATP that provides experts who can extend the capabilities of an organization’s security operations center.
“Through this service, Microsoft will proactively hunt over your anonymized security data for the most important threats, such as human adversary intrusions, hands-on-keyboard attacks, and advanced attacks like cyberespionage—helping your team prioritize the most important risks and respond quickly,” Microsoft explained.
Through this service, users are also provided an “Ask a threat expert” button that they can use to submit questions to Microsoft’s experts.
Microsoft Threat Experts is also available in preview mode and it can be activated from the Windows Defender ATP settings.
Related: Microsoft Launches Azure DevOps Bug Bounty Program
Related: Microsoft Adds New Tools to Azure DDoS Protection
Related: Microsoft Enhances Windows Defender ATP
Related: Microsoft Boosts Azure Security With Array of New Tools