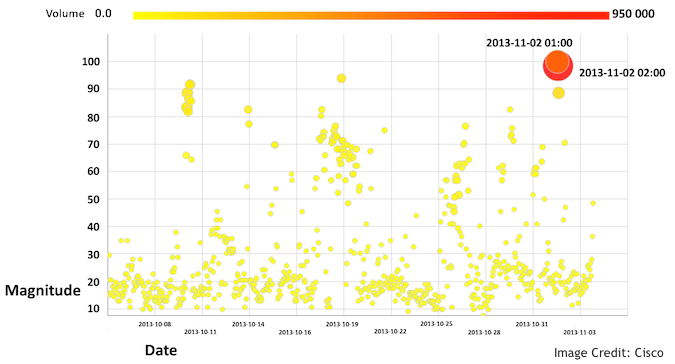
Researchers from Cisco have alerted customers and the Internet community of a massive spike in TCP source port zero traffic that started at 01:00 UTC on Saturday, Nov. 2 and lasted roughly three hours.
According to Cisco, it was was the largest spike of reconnaissance activity they have seen this year.
“Activity was sustained across a significant number of customers for several hours,” a Cisco spokesperson told SecurityWeek.
TCP source port zero serves no legitimate purpose and is a reserved port according to the RFC and it should not be used.
Cisco provided the graph below, which shows the magnitude of the number of its sensors logging scanning activity.
According to Cisco’s Craig Williams, this traffic can be an attempt to identify network security devices.
“Various network equipment will respond to this abnormal traffic differently and an attacker may be able to infer which devices a customer is using to protect their network by inspecting this traffic,” Williams noted in a blog post. “Similarly different operating systems or even different versions of the same operating system may respond to the use of port zero in different ways. This can help enable the attacker to make a more precise attempt to compromise a network.”
Cisco correlated the highest volume of traffic from the IP addresses below, all of which are assigned to Ecatel:
93.174.93.175
80.82.65.237
94.102.63.22
89.248.168.215
89.248.174.80
89.248.160.198
93.174.93.176
89.248.162.236
According to SecurityWeek’s analysis, all IPs listed above point to systems hosted in the Netherlands.
It’s important to consider that while the IPs above should be marked as potentially malicious, reconnaissance IPs are not typically where future associated attacks stem from. In this case, for example, the reconnaissance was conducted from machines in the Netherlands, but if a malicious attacker is behind the effort, attacks would most likely be launched from an entirely different set of IPs from another country.
Security teams should be on the look out for this activity, Cisco advised.
“We do not know the intent of these packets. This could be a simple research project to map portions of the Internet by operating system and service pack or it could be an attacker preparing to do something nefarious,” Williams added.
While any massive scan of the Internet can certainly raise red flags, it does not always represent the planning stages of an attack. However, as Cisco’s Jaeson Schultz noted in an Oct. 13 blog post, “reconnaissance may take place months before the attack begins so look for an increase in scans”.
Cisco advised that network security teams block this port at their firewall, and keep an eye on logs for anomalous behavior. When organizations see port zero activity on their network they should consider the traffic suspicious and investigate the source, Cisco said.
“Administrators should be aware that ongoing transmissions of TCP/IP and UDP packets with a source port of 0 could indicate ongoing attacks, such as spoofing or an attempt to identify a targeted host’s operating system,” Cisco advised in a previously published security activity bulletin.















