Google has shared some interesting data collected by the company from users of its Password Checkup extension for Chrome.
Password Checkup, announced in February, is designed to display a warning to Chrome users whenever they log in to a website using credentials that are known to have been compromised in a third-party data breach. Password Checkup checks the usernames and passwords entered by users against a database containing over 4 billion records.
Google says more than 650,000 have used the extension, and in the first month since its launch it scanned roughly 21 million credentials, of which 1.5%, or 316,000, were marked as unsafe.
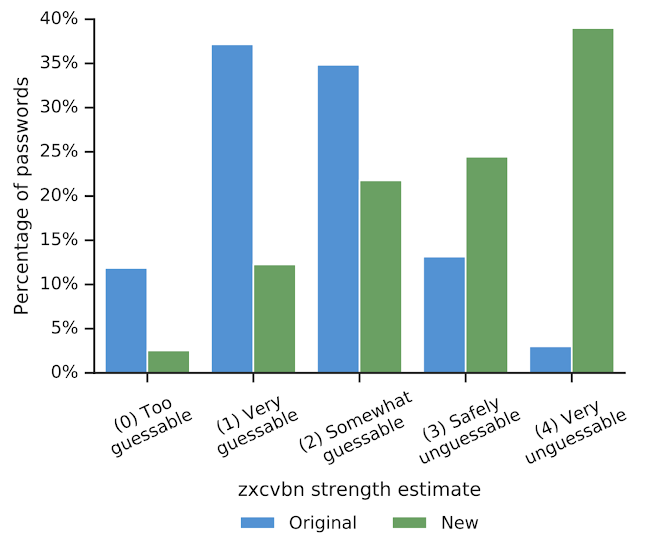
However, data collected by the company shows that only 26% of unsafe passwords have been reset and 60% of the new passwords are strong enough to withstand guessing attacks.
Worryingly, some users have reused compromised passwords for sensitive accounts, including email (0.5%), finance (0.3%), and government (0.2%). The percentage is higher in the case of entertainment (6.3%), news (1.9%), and shopping (1.2%) websites, Google said.
“Outside the most popular web sites, users are 2.5X more likely to reuse vulnerable passwords, putting their account at risk of hijacking,” the tech giant said in a blog post.
Google also announced that it has added two new features to Password Checkup. One allows users to easily send feedback about the extension, while the other gives users more control over their data by allowing them to prevent the tool from sending anonymous telemetry data to Google. This telemetry data includes the number of lookups that reveal unsafe credentials, whether an alert from the extension results in a password reset, and the domain involved.
Researchers at Google and Stanford have also published a paper describing a new protocol where a client can query a data breach repository for specific credentials without revealing the queried information.
When it introduced Password Checkup in February, Google also released the results of a survey of 3,000 Americans. The study showed that 53% of respondents understood the value of including letters, numbers and symbols in their passwords, but only 39% did so, and only 23% believed that password length was important.
Related: Google Warns G Suite Customers of Passwords Stored Unhashed Since 2005
Related: Google Helps G Suite Admins Enforce Strong Passwords
Related: Latest Version of Chrome Improves Password Management, Patches 40 Flaws














