A survey conducted in March by Fortinet shows that over 40% of global cybersecurity incidents affecting organizations with operational technology (OT) systems resulted in outages that put physical safety at risk.
The results of the survey are found in Fortinet’s 2022 State of Operational Technology and Cybersecurity report. More than 500 OT professionals across 28 countries in the Americas, Western Europe, the APAC region, and a handful of African and Middle Eastern countries took part in the survey.
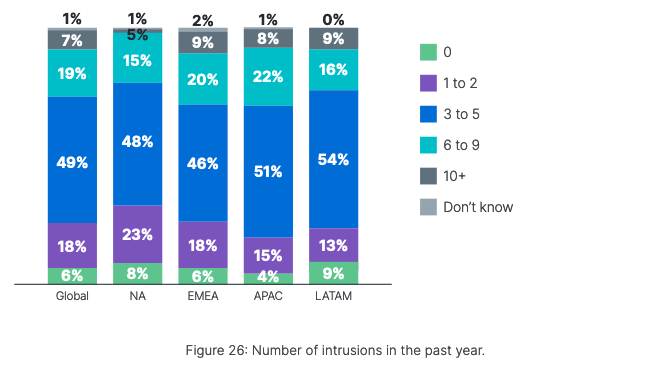
The report shows that 93% of OT organizations had experienced at least one cybersecurity incident in the past 12 months, and more than three-quarters admitted suffering at least three intrusions.
The most common types of attacks involved malware and phishing, but Fortinet pointed out that these types of incidents have significantly declined in North America — along with insider breaches — compared to the previous year.
Globally, 61% of respondents said incidents impacted only OT systems or both OT and IT systems. In addition, nearly half of respondents said their organization suffered an operational outage that affected productivity. Forty-two percent of incidents resulted in an operational outage that put physical safety at risk, and the percentage exceeds 50% in Latin America.
Operational outages impacting revenue, loss of business-critical data, failure to meet compliance requirements, and a negative impact on the brand were reported by roughly 30% of respondents, for each category.
Learn More About OT Security at SecurityWeek’s ICS Cyber Security Conference
Half of respondents said it took them hours to restore impacted systems and 31% said it took them days. In some cases, it took organizations weeks and even months to restore services, but it took some of the more mature organizations only minutes to get systems back online.
Of the respondents in North America, roughly a quarter reported being hit by ransomware in the past year, but three-quarters said they were concerned about ransomware more than other types of threats.
When it comes to security posture, Fortinet’s survey saw an improvement compared to the previous year, but more still needs to be done.
Globally, only 13% have centralized visibility of all OT activities and only 52% of organizations have security operations center (SOC) teams that can monitor and track all OT activities.
Related: Increasing Number of Threat Groups Targeting OT Systems in North America
Related: 7 Steps to Start Reducing Risk to Your Critical Infrastructure Quickly
Related: Many Industrial Firms Say Cybersecurity Systems Cause Problems to Operations












