Despite an increase in cybersecurity incidents, many industrial organizations turn off security systems if they interrupt or otherwise impact operations, according to a global survey conducted earlier this year by Kaspersky.
Kaspersky reported recently that it only saw a small increase in the percentage of industrial control system (ICS) computers targeted in 2021, compared to the previous year.
However, of the more than 300 respondents who took part in the latest survey, half reported seeing an increase in security incidents affecting ICS or other operational technology (OT) systems since the end of 2019.
In the past year, nearly one-third of the organizations that took part in the survey experienced a high number of incidents (at least 20). These incidents are often related to staff violating IT security policies, devices getting infected with malware, or employees inappropriately using IT resources.
[ Learn more about securing ICS/OT at SecurityWeek’s ICS Cyber Security Conference ]
While many organizations have come to understand the importance of securing their OT environments, 40% of respondents admitted that the security tools they are currently using are not compatible with their automation systems, and 38% reported at least one event where cybersecurity products interrupted or in some way affected their operations.
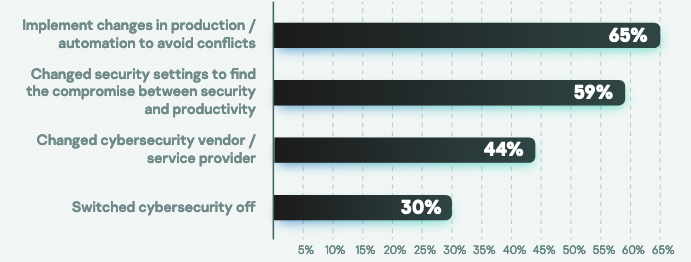
When they experienced these disruptions, 30% of companies decided to turn off their security systems. Others made changes to production or automation systems to avoid conflicts, they changed security settings in an effort to find a balance between security and productivity, or they switched cybersecurity vendors.
In some cases, compatibility issues between OT and security systems arise due to the inability to upgrade OT. Companies are often stuck with outdated products due to the fact that vendors don’t offer newer versions.
“In the past asset owners reasonably assumed that the protection and automation systems responsible for the core business processes of an industrial organization would be left undisturbed throughout the equipment’s lifetime, lasting decades – with the possible exception of occasional settings changes. It was common practice to commission systems as a whole and perform complete retesting and recommissioning if any changes were to be made,” explained Kirill Naboyshchikov, business development manager for Kaspersky Industrial CyberSecurity.
Naboyshchikov added, “However, with the introduction of next generation digital automation systems, there are many instances where this may no longer be the case. Therefore, both general purpose and ultra-specialized computer-based automation systems should be equipped with the following security subsystems and tools and processes: a vendor-approved, holistic and centrally managed protection system; permanent vulnerability monitoring and compliance scanning; network intrusion and anomaly detection; and update, patch management and version control.”
Additional information, along with recommendations for improving OT security, is available in the “Kaspersky ICS Security Survey 2022” (PDF).
Related: Kaspersky Sees Rise in Ransomware Attacks on ICS Devices in Developed Countries
Related: Europe Warned About Cyber Threat to Industrial Infrastructure












