Researchers at Netcraft have come across a Facebook phishing attack in which malicious actors leveraged some clever methods to increase their chances of tricking users into handing over their credentials.
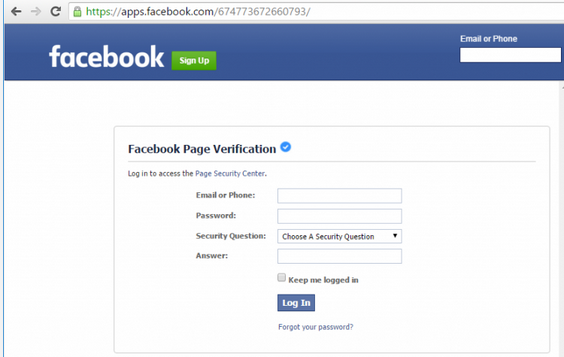
The phishing page, designed to look like a Facebook page verification form, is served via the social media giant’s app platform. The attackers created an app that serves content (i.e. the phishing page) from an external website via an iframe.
By launching the attack from Facebook’s app platform, cybercriminals trick victims into thinking that the phishing page is hosted on the legitimate facebook.com domain. Since the attack leverages Facebook’s own TLS certificate and since the external website serving the malicious content also uses HTTPS, the browser’s address bar shows the padlock icon and no warnings are displayed.
When users access the phishing page, they are instructed to enter their email address or phone number, password, and provide the answer to their security question. The collected information is sent directly to the attacker’s website.
Another clever trick is used by cybercriminals to avoid raising suspicion. When the information is first submitted on the phishing page, an error message is displayed, informing the user that the username or password are incorrect.
“A suspicious user might deliberately submit an incorrect username and password in order to test whether the form is legitimate, and the following error message could make them believe that the credentials really are being checked by Facebook,” explained Netcraft’s Paul Mutton.
After the credentials are entered a second time, the victim is told to wait up to 24 hours for the submission to be approved. In the meantime, the cybercriminals can access the compromised account themselves or they can sell it to other malicious actors who can abuse it for spam or various types of scams. The hijacked account can also be used to lure the victim’s friends to the phishing page.
Mutton pointed out that users can protect themselves against such attacks by enabling two-step verification on their Facebook account. Furthermore, the login alerts feature provided by Facebook notifies users when their account has been accessed from an unknown device.
Regular users are often advised by experts to check the browser’s address bar for the “https” string and the padlock icon to ensure that they are on the legitimate website and not a phishing page. However, malicious actors have been improving their techniques in an effort to increase their chances of success.
A good example of how cybercriminals can trick users into believing that they are on a legitimate website is provided by the banking Trojan GozNym. The malware uses web injections to display phishing pages on top of legitimate bank websites. In order to make it look like the phishing page is hosted on the bank’s official domain and ensure that the browser displays the SSL certificate indicator, the malware sends empty requests to the bank’s website in order to keep the SSL connection alive.
Related: More Than 1 Million Users Access Facebook Over Tor
Related: Researcher Finds Malicious Web Shell on Facebook Server
















