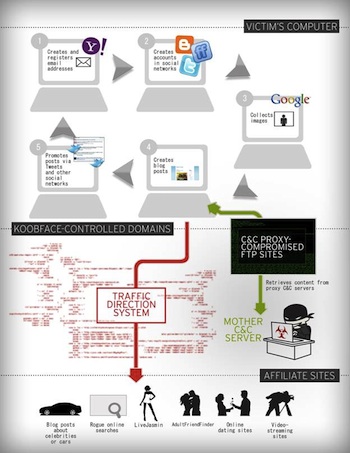
KOOBFACE Gang Upgraded Botnet Framework With a Sophisticated Traffic Direction System (TDS) that Handles Traffic Referenced to Affiliate Sites.
The Koobface crew is at it again, and this time may be branching out into a new business.
According to researchers at Trend Micro, the Koobface crew has designed their own traffic direction system (TDS) to aid in their operations and possibly offer the system as a service to others. The gang’s TDS handles all the traffic referenced to their affiliate sites, which combined with new binary components increase the amount of traffic headed to their TDS and creates a bigger profit.
“The KOOBFACE gang’s TDS redirected traffic to advertising sites from which they earn referral money or to several of their affiliate sites,” blogged Jonell Baltazar, senior threat researcher at Trend Micro. “Note that websites that use the referral business model such as advertising and affiliate sites earn more as the Internet traffic to their sites increases.”
 Some may remember that researchers with the Information Warfare Monitor initiative revealed that the Koobface gang made more than $2 million between June 2009 and June 2010 using pay-per-click and pay-per-install affiliate programs and compromising computers with rogue antivirus. Though the gang is best known for targeting social networking sites such as Facebook, the group also abuses blogging platforms by uploading content designed to increase the search engine optimization ranking of the botnet’s affiliate sites. The posts also contain obfuscated JavaScript code that references the botnet’s TDS domain.
Some may remember that researchers with the Information Warfare Monitor initiative revealed that the Koobface gang made more than $2 million between June 2009 and June 2010 using pay-per-click and pay-per-install affiliate programs and compromising computers with rogue antivirus. Though the gang is best known for targeting social networking sites such as Facebook, the group also abuses blogging platforms by uploading content designed to increase the search engine optimization ranking of the botnet’s affiliate sites. The posts also contain obfuscated JavaScript code that references the botnet’s TDS domain.
“This allows the TDS to track the number of visits to each blog post and to redirect visitors to the botnet’s affiliate sites,” Baltazar blogged. “The botnet makes money from the clicks victims make while reading blog posts and from the traffic the TDS directs to designated final landing sites.”
The traffic redirects seem to be based on specific keywords, such as “cars,” “porn” or “celebrity.” According to Nart Villeneuve, senior threat researcher for Trend Micro, the fact that the Koobface gang is now running their own TDS means they probably either are – or plan to – provide this service for other botnet operators.
“TDS are commonplace in the porn industry,” Villeneuve told SecurityWeek. “They are used as a monetization mechanism by botnet operators. So, botnet operators do not always run the TDS system, but are affiliates of the TDS operators who pay the botnet operators for the traffic they deliver.”
The new TDS allows the gang to earn more, Baltazar explained, by providing the Koobface crew a way to more efficiently target celebrity fans, online daters, porn surfers and others. Their TDS allows them to handle the increase in the number of unwitting users who land on specially-crafted blog posts that lead to various advertising, click-fraud and other affiliate sites, he continued.
“The KOOBFACE gang is clearly still up to no good and will most probably continue victimizing users,” Baltazar blogged. “As such, we advise their target platforms to push through with efforts to avoid bot-automated interactions and to implement stricter security measures to protect their users from cybercriminal abuse.”















