KBOT, a piece of malware that has been infecting computers for the past year, has been classified by Kaspersky as a “living virus,” a class of malware thought to be extinct.
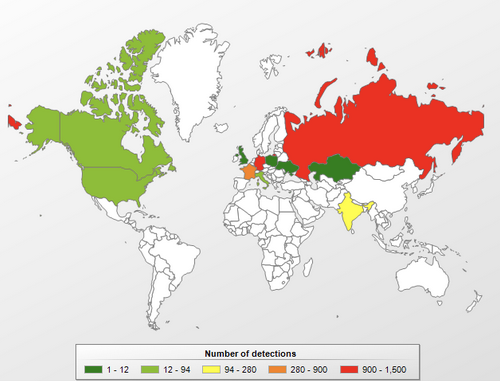
Kaspersky discovered KBOT, which is also known as Kpot, in February 2019, and between March and December 2019 the company detected thousands of infections. A majority of infections were spotted in Russia, followed by Germany, France, India and North America.
The cybersecurity firm told SecurityWeek that it has already detected 1,880 unique files infected by KBOT in 2020.
Kaspersky says KBOT is the first virus seen in the wild in recent years. The company previously observed the Expiro and Sality viruses, but these threats were not as widespread and did not have such a wide range of capabilities as KBOT, which appears to be designed for stealing information from compromised machines.
Viruses are a type of malware that spread by injecting their code into other programs on the infected system.
“A living virus is a rarity as they have been thought to be extinct as a class of malware. Seeing a virus as a serious, actual threat is quite unusual,” Anna Malina, security researcher at Kaspersky, told SecurityWeek.
KBOT can infect a computer via the internet, the local network or from removable drives. Once it has infected a device, KBOT attempts to become persistent by writing itself to the Startup folder and the Windows Task Scheduler. The virus then leverages web injects to steal user data from browsers, including passwords, cryptowallets, and payment cards.
“KBOT is able to spread quickly in the system and the local network by infecting executable files with no possibility of recovery, bringing a lot of damage to the infected device,” Malina said via email.
A variant of KBOT was also analyzed last year by Russian antivirus company Dr. Web and Proofpoint, but they did not mention its virus-like capabilities. Proofpoint reported at the time that the malware, named Kpot 2.0, had been offered on various underground hacking forums for roughly $100.
A blog post published this week by Kaspersky describes in detail how KBOT works.
Related: Coronavirus-Themed Emails Deliver Malware, Phishing, Scams
Related: Echobot Malware Drives Significant Increase in OT Attacks
Related: Targeted Attacks Deliver New “Anchor” Malware to High-Profile Companies















