Kaspersky Lab researcher Vitaly Kamluk has released the source code of Bitscout, a compact and customizable tool designed for remote digital forensics operations.
Bitscout, which is not an official Kaspersky product, initially started as a hobby project a few years ago, and it has been continually improved based on the requirements that arose in Kaspersky investigations involving digital forensics.
Bitscout 2.0 – version 1.0 was never released to the public – enables forensic investigators to remotely analyze a system, while allowing the system’s owner to monitor the expert’s activities and ensure that their access is limited to the targeted disks. The tool can be useful to researchers, law enforcement cybercrime units, and educational institutions.
The owner of the system on which forensic analysis will be conducted is provided an image file that they must burn onto a removable storage drive. The system is then booted from this drive and the investigator connects remotely to Bitscout over SSH using a VPN.
Bitscout includes several popular tools designed for forensic analysis, but users can also customize them or add their own. The tool uses a text-based user interface (TUI) in order to make it easy to operate.
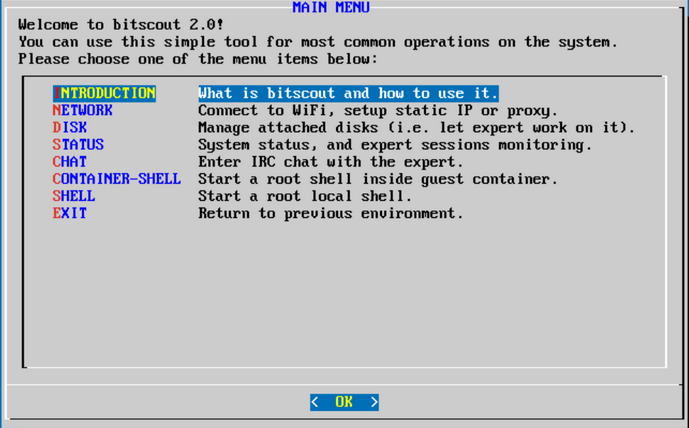
According to Kamluk, the investigator is only provided root privileges inside a virtual container, and the owner can specify which disks can be analyzed to prevent unauthorized access. On the other hand, the researcher can install additional software and make changes to the system from this container, but only in the volatile memory to ensure that everything is restored to its initial state after the device is shut down.
“All remote sessions are recorded and stored outside of the container,” Kamluk said in a blog post. “This provides a good level of isolation and a way to reconstruct the forensic process for learning purposes, or prove the existence of evidence.”
The Bitscout source code and basic usage instructions are available on GitHub.
Related: Cisco Releases Open Source Malware Signature Generator
Related: Google Launches OSS-Fuzz Open Source Fuzzing Service
Related: Netflix Releases Open Source Security Tool “Stethoscope”













