Intel Patches for Meltdown and Spectre Cause More Frequent Reboots
Intel on Wednesday shared information on the performance impact of the Meltdown and Spectre patches on data centers, and the company told customers that systems with several types of processors may experience more frequent reboots after firmware updates are installed.
Performance impact on data centers
Roughly one week ago, Intel informed customers that the mitigations for the recently disclosed CPU flaws should have a negligible performance impact for operations typically conducted on home and business PCs. The company reported seeing performance penalties ranging from 2-14% on these types of systems.
Intel has also conducted some performance tests on data centers and the initial results show that, as expected, impact depends on the type of workload and the configuration of the system.
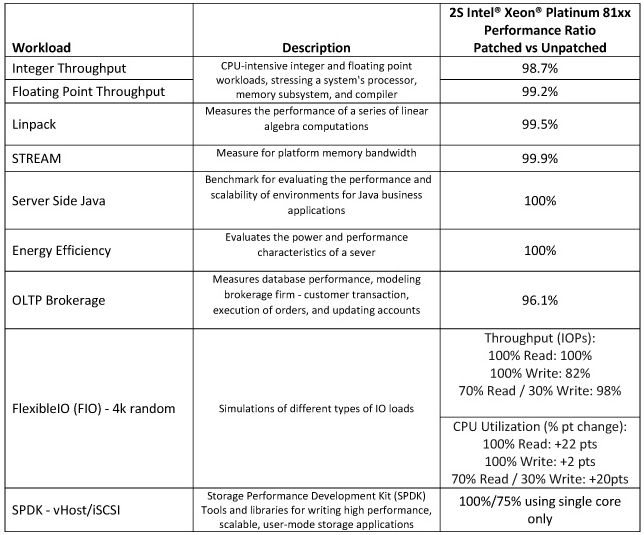
Tests conducted on Intel Xeon Scalable (Skylake) systems showed that impact on integer and floating point throughput, Linpack, STREAM, server-side Java, and energy efficiency, which are typical for enterprise and cloud customers, was 0-2%.
In the case of online transaction processing (OLTP), Intel saw a performance impact of roughly 4%. The company is in the process of conducting more tests and believes the results will depend on system configuration and other factors.
In the case of FlexibleIO, which simulates various I/O workloads, throughput performance decreased by 18% when the CPU was stressed, but there was no impact when CPU usage was low.
Intel saw the most significant performance penalties during Storage Performance Development Kit (SPDK) tests, specifically using iSCSI, reaching 25% when only a single core was used. However, there was no impact on performance when SPDK vHost was used.
Microsoft, AWS, Red Hat and others have also shared information on the impact of the Spectre and Meltdown mitigations on performance.
Firmware updates cause reboots
Intel has released firmware updates for 90% of the CPUs released in the last five years. While the company claims that the updates are effective at mitigating the Spectre and Meltdown attacks, users have reported seeing more frequent reboots after applying patches.
Intel initially said only systems running Broadwell and Haswell CPUs experienced more frequent reboots, but similar behavior has also been reported on Ivy Bridge-, Sandy Bridge-, Skylake-, and Kaby Lake-based platforms.
“We have reproduced these issues internally and are making progress toward identifying the root cause. In parallel, we will be providing beta microcode to vendors for validation by next week,” said Navin Shenoy, executive vice president and general manager of Intel’s Data Center Group.
Many affected vendors, including system manufacturers, have already released patches and workarounds for the Spectre and Meltdown vulnerabilities, but installing them has been known to cause serious problems.
Microsoft’s initial patches prevented systems with some AMD processors from booting, and Canonical’s Meltdown fix broke some devices running Ubuntu. Industrial control systems (ICS) vendors have warned customers that the patches for the CPU vulnerabilities should be thoroughly tested before being installed in order to prevent any disruptions.
Related: Lawsuits Filed Against Intel Over CPU Vulnerabilities
Related: Fake Meltdown/Spectre Patch Installs Malware
Related: Oracle Fixes Spectre, Meltdown Flaws With Critical Patch Update












