Intel patched 226 vulnerabilities in its products last year, according to data from the 2021 Product Security Report released by the chip giant on Thursday.
Intel last year said it had paid out an average of $800,000 per year through its bug bounty program since it was launched in 2018, and the company told SecurityWeek this week that the average yearly amount has remained the same, which means payouts should now total more than $3 million.
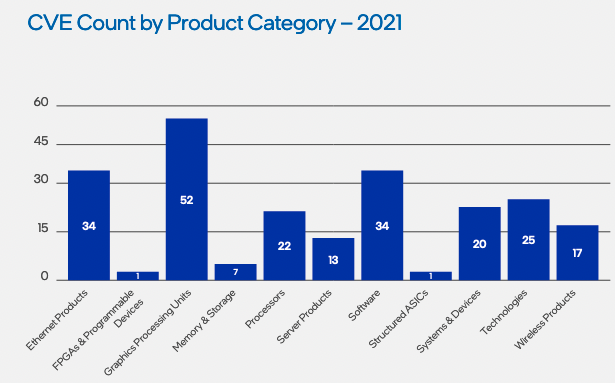
Of the 226 security holes fixed in 2021, half were discovered internally and 43% were reported through its bug bounty programs — the rest came from open source projects managed by Intel and organizations that cannot seek bug bounties. The number of resolved flaws is roughly the same as in 2019 (236) and 2020 (231).
A majority of the high-severity issues reported through the bug bounty program affected GPUs and processors. As for internally-discovered issues, Ethernet products are at the top.
Overall, only two vulnerabilities discovered in 2021 were rated “critical” and 52 were rated “high severity” — nearly 150 were classified as “medium severity.”
Intel hosted its bug bounty program on the HackerOne platform until December 2021, when it transitioned to Intigriti. The company is currently offering up to $100,000 for “critical” and “exceptional” vulnerabilities.
Intel this week also announced expanding its bug bounty program with a project named Circuit Breaker, which brings together “elite hackers” to hunt for vulnerabilities in the company’s products. The project involves hosting multiple limited-time events that focus on specific new technologies and platforms.
The first event, which focuses on 11th Gen Core processors, started in December and it will run until May.
Related: Intel CPU Vulnerability Can Expose Cryptographic Keys
Related: Intel, AMD Patch High Severity Security Flaws
Related: Intel Releases 29 Advisories to Describe 73 Vulnerabilities Affecting Its Products
Related: Intel Patches Tens of Vulnerabilities in Software, Hardware Products

