New Threat Detection Marketplace Connects AV Companies and Enterprises to Improve Protection Coverage Against New Threats
Stable version 1.0 of PolySwarm has been reached, and will be announced within the next couple of weeks. It is a new approach to suspect file threat intelligence sharing, using collective wisdom (or swarm intelligence) and blockchain to pronounce and disseminate judgement on suspicious files. In some ways it is similar to VirusTotal, but with major differences: it adds the collective wisdom of independent malware analysts — and rewards them. It has been described as VirusTotal on steroids.
Any new approach to a problem presupposes weakness in the existing approach. PolySwarm sees weaknesses in the organization of the anti-malware industry (not the anti-malware companies, but the market) and in VirusTotal. The weakness in the market is the repetition of effort. Dozens of separate companies employ dozens of highly skilled analysts to study the same suspect files. This is simply an inefficient use of the industry’s resources.
The problem with VirusTotal comes in two undesirable side-effects. The first is that it promotes the potential for false positives. Files submitted to VirusTotal are not analyzed by human analysts but are subject to the anti-malware engines of all the leading anti-malware companies. Mistakes can be made. A benign file can be flagged as malicious. If two or three engines determine a file to be malicious, there is pressure on the remaining companies to do similar or appear to be laggardly — even if it is a false positive.
The second problem with VirusTotal is that it restricts the anti-malware market — it implies that the anti-malware market comprises solely the big companies that add their engines to VirusTotal. In reality there may be thousands of very small companies and independent experts with specialist knowledge in specific areas around the world. These tend not to get involved with VirusTotal because they get little from it.
“As malware attacks continue to grow and evolve,” explains Steve Bassi, CEO of PolySwarm, “we need a new way to protect enterprises from threats. The existing AV model of single vendor threat detection is inefficient, there are too many false detections and it’s designed to focus on known, widespread threats. Ultimately this slower model of malware discovery puts users at risk. Added to this, the industry’s also struggling with a shortage of skilled security talent which is why we believe it’s time for a re-think on the economics of this industry.”
PolySwarm seeks to provide an additional and alternative approach by creating a decentralized open market for suspicious file intelligence, bringing together the mainstream existing anti-malware vendors, worldwide small companies and independent experts, and financial incentive rewards, under blockchain and smart contracts built on the Ethereum platform. The rewards come via PolySwarm’s own cryptocurrency, Nectar (NCT).
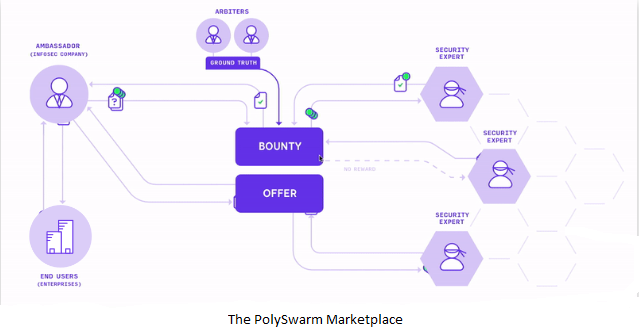
There are four key groups associated with the PolySwarm threat intelligence market: enterprises, ambassadors, arbiters and experts. Two additional terms are involved: artifacts and bounties. Enterprises are the end users with suspect or worrying artifacts (currently just files, but planned to include URLs, domains and emails). The ambassadors are — for the time being at least — the existing mainstream anti-malware vendors. Bounties are the rewards offered by the ambassadors and earned (or not) by the experts — the many thousands of independent (or micro company) malware specialists around the world. Many of these experts will have developed their own micro-engines to help categorize files in specialist areas.
These experts deliver assertions — malign or benign — on the artifacts put forward by the ambassadors. The arbiters are the referees, who give final judgement on the assertions.
It works, described simplistically, like this: the enterprise submits a suspect file to its anti-malware vendor (an ambassador). The vendor has already delivered its decision in the normal course of operation — but the user is not convinced. The vendor can then either commit internal resources to further analyze the file, or it can submit it to the PolySwarm market.
Submitting it to the market requires a bounty. Let’s say that the ambassador offers three NCT coins for a correct assertion from the experts. This becomes the ‘pot’. Experts who believe they know the answer can respond with either a ‘benign’ or ‘malign’ assertion; but to do so they must stake their own NCT amount, which is added to the pot. The more confident they are, the more they can stake. If correct, they will receive back their stake plus a percentage of the pot (a percentage based on the ratio between their own stake and bounty plus all expert stakes).
This approach encourages experts who are confident, and discourages flippant responses (those experts who are wrong will lose their stake). The final decision on correct assertions and payment amounts comes from the arbiters. The result is that companies and MSSPs with large volumes of incoming files, network traffic or URLs can obtain a near real-time verdict on the maliciousness of these files through PolySwarm’s automated marketplace.
Bill Fehr, PolySwarm’s vice president of growth and partnership, told SecurityWeek that there are three core PolySwarm benefits. “Firstly, end users will be better protected by the interweaving and overlapping coverage provided by many engines/micro-engines looking for threats on PolySwarm. Secondly, threat detection engines will financially stake their convictions for better quality, and will financially benefit from accuracy. Thirdly, the economics of the marketplace encourages some engines to specialize to get closer to detecting threats at day zero.”
Like any marketplace, PolySwarm depends upon supply and demand. The demand side comprises the thousands of new malware samples generated every day and submitted via the ambassadors. Initially the ambassadors will be limited to existing malware vendors because they have the greatest incentive to recognize new malicious files. As the market grows, other ‘ambassadors’ will be attracted; and since it is an open market, nobody is excluded. The supply side comes from those expert micro-engines joining the market — they supply the threat intelligence.
“The PolySwarm network is a highly innovative concept which decentralizes evaluation of myriad cyber security threat objects”, said Samir Mody, expert threat researcher at K7 Security, one of the initial ‘arbiters’ in the system. “The PolySwarm ecosystem thus actively engages and rewards talented cyber experts, with disparate specialized skill-sets, from across the world who would otherwise not have had opportunities to contribute to global cyber safety.”
“PolySwarm is pushing the boundaries of threat detection by economically rewarding us to accurately detect malware” added Mario Bono, head of the malware lab at Ikarus. “The ability to generate passive income in addition to accessing a vast stream of new malware samples to improve our products is what has drawn us to PolySwarm’s marketplace.”
Related: U.S. Cyber Command Shares Malware via VirusTotal
Related: Chronicle Unveils VirusTotal Enterprise
Related: False Positive Alerts Cost Organizations $1.3 Million Per Year: Report
Related: With Security at the Foundation, Blockchain Can Revolutionize the World















