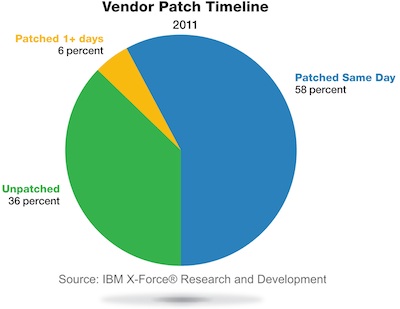
Attackers are adapting their techniques as software vendors get better at patching vulnerabilities, according to a new report from IBM. In its X-Force 2011 Trend and Risk Report, IBM notes that the amount of vulnerabilities left unpatched in 2011 dropped to 36 percent from 43 percent in 2010. But improvements in securing Web applications may have led attackers to change tactics, sparking an increase in automated password guessing and shell command injection attacks against Web servers, the firm reported.
“In 2011, we’ve seen surprisingly good progress in the fight against attacks through the IT industry’s efforts to improve the quality of software,” said Tom Cross, manager of Threat Intelligence and Strategy for IBM X-Force, in a statement. “In response, attackers continue to evolve their techniques to find new avenues into an organization. As long as attackers profit from cyber crime, organizations should remain diligent in prioritizing and addressing their vulnerabilities.”
 Improvements in application security are behind a 50 percent drop in cross-site scripting attacks, according to the report. There was also a 30 percent drop in the number of exploits released in 2011 compared to the average amount seen during the last four years.
Improvements in application security are behind a 50 percent drop in cross-site scripting attacks, according to the report. There was also a 30 percent drop in the number of exploits released in 2011 compared to the average amount seen during the last four years.
Despite this good news however, SQL injection remained one of the most problematic classes of vulnerabilities on the Web. In addition, towards the end of the year, the X-Force team witnessed two to three times more shell command injection attack activity than was seen in earlier in the year.
“Shell Command Injection vulnerabilities allow attackers to execute command-line instructions to gain control of a web server,” blogged X-Force’s Leslie Horacek. “With complete control over the content of the website, attackers then have the ability to modify the site so that visitors are redirected to exploits that install malware on their machines. Or, attackers can use the compromised web servers to act as a jump pad from which they can further target other systems and networks.”
Attackers are also taking advantage of poor passwords and password policies, she wrote, adding that there is no shortage of automated attack activity on the Web in which cyber-criminals are scanning for systems with weak logins. IBM observed a large spike in this activity directed at secure shell servers (SSH) in the latter half of 2011, she added.
“Enterprises around the world continue to face tremendous challenges running their businesses and protecting their assets in an increasingly connected world,” she blogged. “But as this report’s data shows, a somewhat contradictory course is unfolding, just as attackers are coming on full force in 2011, so too have the improvements in computer security in 2011 as companies have begun embracing better practices.” The full report can be accessed here.
Related Reading: Hacktivism Is The Rising Cause of Data Breaches, Verizon Finds
Related: Endless Exploit Attempts Underline Importance of Timely Java Patching












