Hackers have been scanning the Internet for Cisco Small Business routers affected by information disclosure and command injection vulnerabilities that were patched only days ago by the networking giant.
Cisco informed customers on January 23 that its Small Business RV320 and RV325 routers are affected by two high-severity flaws. One of them, tracked as CVE-2019-1653, has been described as an information disclosure vulnerability that can be exploited by an unauthenticated attacker to remotely obtain sensitive information from a device, including router configuration and detailed diagnostic information.
 The second vulnerability, identified as CVE-2019-1652, allows an attacker with admin privileges to execute arbitrary commands as root. These vulnerabilities can be combined to take control of an affected router.
The second vulnerability, identified as CVE-2019-1652, allows an attacker with admin privileges to execute arbitrary commands as root. These vulnerabilities can be combined to take control of an affected router.
The first issue impacts routers running versions of the firmware 1.4.2.15 and 1.4.2.17, and it has been patched in version 1.4.2.19. The second weakness affects versions 1.4.2.15 through 1.4.2.19, and it has been fixed in 1.4.2.20.
RedTeam Pentesting, the Germany-based company whose researchers discovered these flaws, released details and proof-of-concept (PoC) code at around the time Cisco’s advisories were published.
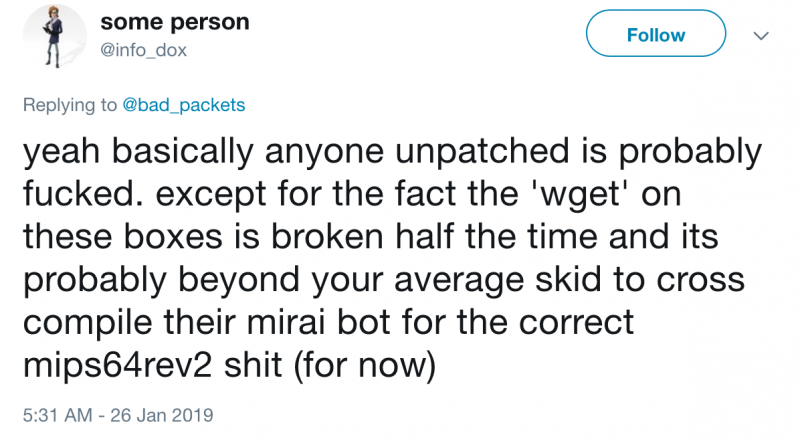
On January 25, researcher David Davidson (aka @info_dox and 0x27) published PoC exploits for both CVE-2019-1652 and CVE-2019-1653. The exploits leverage CVE-2019-1653 to obtain configuration and debug files, which contain authentication data for the web interface of Small Business RV320 and RV325 routers. The configuration data includes hashed passwords, and the debug files include /etc/shadow, which stores encrypted passwords.
Once the passwords have been obtained, an attacker can log in to the router and execute arbitrary commands on the underlying Linux shell with root privileges using CVE-2019-1652.
Bad Packets Report has been monitoring what it has described as “opportunistic scanning activity” aimed at exploiting CVE-2019-1653.
“These scans consisted of a GET request for /cgi-in/config.exp which is the path that allows unauthenticated remote users to obtain an entire dump of the device’s configuration settings,” explained Bad Packets’ Troy Mursch.
A scan conducted by Bad Packets using data from BinaryEdge revealed that over 9,600 Cisco RV320 and RV325 routers across more than 120 countries are affected by CVE-2019-1653.
The highest number of impacted devices, roughly 4,400, has been identified in the United States, followed by Canada (780), Brazil (630), and Thailand (300).
Once attackers have identified vulnerable devices and exploit CVE-2019-1653, they can leverage CVE-2019-1652 to execute arbitrary commands and take control of the routers.
Cisco has updated its advisories to inform users that exploit code is publicly available and that the Internet has been actively scanned in search of vulnerable devices.
Related: Cisco Warns of Zero-Day Vulnerability in Security Appliances
Related: Default Account Exposes Cisco Switches to Remote Attacks














