Researchers have shown how hackers could silently exfiltrate sensitive information from air-gapped computers by manipulating the brightness of their screen.
The research was carried out by experts from Israel’s Ben-Gurion University of the Negev and the Shamoon College of Engineering. Researchers from Ben-Gurion University previously demonstrated how hackers could exfiltrate data from air-gapped systems via power lines, magnetic fields, infrared cameras, router LEDs, scanners, HDD activity LEDs, USB devices, the noise emitted by hard drives and fans, and heat emissions.
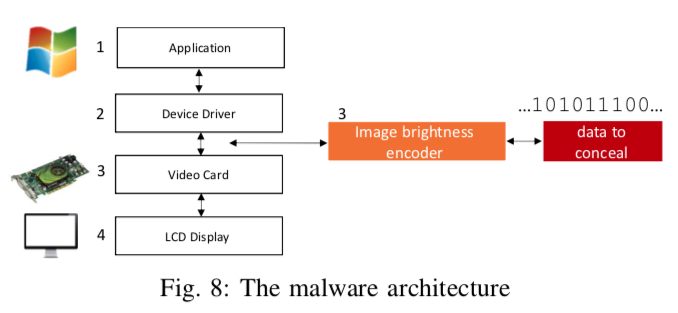
This time they showed how a piece of malware could collect valuable data from a device (e.g. passwords, encryption keys, files), modulate it in screen brightness, and transmit it to a nearby camera.
As with most attacks aimed at air-gapped systems, an attacker would have to find a way to plant malware on the targeted device, and they would also have to find a way to recover the data in real time from the compromised machine, for example by hacking existing security cameras or webcams. While these requirements may not be easy to achieve for many hackers, a determined and well-resourced adversary could surely pull it off.
The researchers have proposed modulating harvested data by assigning a “1” value to a certain screen brightness and a “0” value to a different brightness. Quickly changing the screen brightness results in a sequence of bits that can be captured by a camera pointed at the screen.
While it may seem that a screen whose brightness keeps changing would attract attention, the experts determined that it’s enough to change the red color of each pixel by only 3%. This small change in brightness is not visible to the naked eye, but it can be captured by a camera, which allows the exfiltration process to take place even while a user is working on the targeted computer.
The attack was tested using two displays — a 24” PC monitor from Dell and a 40” LED TV from Samsung — and three types of cameras, namely a Sony security camera, a Microsoft webcam, and the camera of a Samsung Galaxy S7 smartphone.
The security camera and the webcam performed the same. They captured data from up to 9 meters (30 feet) at a bitrate ranging between 5 to 10 bits per second. The smartphone camera only worked over distances of up to 1.5 meters (5 feet) with a bitrate of 1 bit per second. The researchers have pointed out that the room where they conducted the experiments only allowed for a maximum distance of 9 meters between the screen and the cameras, but the attack likely works over longer distances as well.
The researchers have published a paper detailing their work and they have also made available a video that shows the efficiency of this exfiltration method.
Related: Hackers Can Steal Cryptocurrency From Air-Gapped Wallets














