Google has released updates to address multiple vulnerabilities in the Chrome browser, including two that are actively exploited in attacks.
Chrome 86.0.4240.183 for Windows, macOS, and Linux was pushed to the stable channel with patches for a total of seven vulnerabilities, all of which feature a severity rating of high.
The bugs include CVE-2020-16004 (use after free in user interface), CVE-2020-16005 (insufficient policy enforcement in ANGLE), CVE-2020-16006 (inappropriate implementation in V8), CVE-2020-16007 (insufficient data validation in installer), CVE-2020-16008 (stack buffer overflow in WebRTC), and CVE-2020-16011 (heap buffer overflow in UI on Windows).
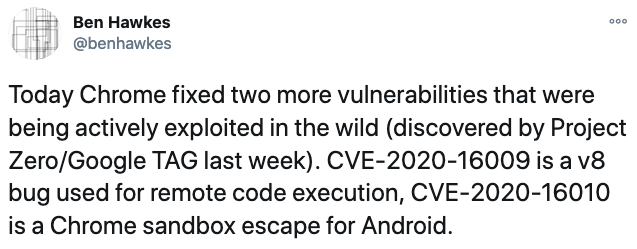
The seventh of the vulnerabilities is CVE-2020-16009, described as inappropriate implementation in the V8 JavaScript engine. Google warns that an exploit for the flaw already exists in the wild.
Discovered by Clement Lecigne of Google’s Threat Analysis Group and Samuel Groß of the Project Zero team, the zero-day vulnerability can be exploited via a crafted HTML page to corrupt memory and eventually achieve arbitrary code execution.
To exploit the flaw, an attacker would have to trick the victim into accessing the malicious page. In fact, all of these bugs can be exploited for code execution or system compromise by getting a user to access a malicious webpage.
Less than two weeks ago, Google released patches for other high-severity flaws in Chrome, including CVE-2020-15999, an actively exploited zero-day in FreeType.
This week, Google also announced the availability of a patch for CVE-2020-16010, a high-severity flaw impacting Chrome for Android, which has also been exploited in the wild.
The issue, a heap buffer overflow in the UI on Android, was discovered by Maddie Stone, Mark Brand, and Sergei Glazunov of Google Project Zero. Chrome 86.0.4240.185 for Android addresses the flaw.
Google Project Zero’s Ben Hawkes noted on Twitter that both vulnerabilities were identified last week.
Google said it awarded $36,000 in bug bounty rewards to the researchers who discovered the newly addressed vulnerabilities. However, the company did not provide details on the amount paid for CVE-2020-16008 and notes that no bounty was awarded for the two actively exploited flaws.
Related: Chrome Update Patches Actively Exploited FreeType Vulnerability
Related: Chrome Vulnerabilities Expose Users to Attacks Via Malicious Extensions
Related: Chrome Sandbox Escape Vulnerability Earns Researchers $20,000














