Organizations hit by attacks exploiting a recently disclosed zero-day vulnerability affecting the GoAnywhere managed file transfer (MFT) software have started coming forward and disclosing impact.
The vulnerability, tracked as CVE-2023-0669, was disclosed by GoAnywhere developer Fortra on February 1, after the company became aware of in-the-wild exploitation. Mitigations and indicators of compromise (IoCs) were released immediately, but a patch was only made available a week later.
Information about the attacks exploiting CVE-2023-0669 and victims of these attacks are now coming to light.
In a filing with the US Securities and Exchange Commission (SEC), Community Health Systems (CHS), one of the largest healthcare services providers in the United States, revealed that a “security breach experienced by Fortra” resulted in the exposure of personal and protected health information (PHI) belonging to patients of CHS affiliates.
The organization is conducting an investigation, but it currently estimates that roughly one million individuals may have been impacted by the incident. CHS said the breach does not appear to have had any impact on its own information systems and business operation, including the delivery of patient care.
A source told SecurityWeek that several major companies have been hit by the GoAnywhere zero-day attacks and it’s only a matter of time before they disclose significant breaches.
Cybersecurity firm Huntress reported last week that it had investigated an attack apparently exploiting CVE-2023-0669 and managed to link it to a Russian-speaking threat actor named Silence. This group has also been tied to TA505, a threat group known for distributing the Cl0p ransomware.
Indeed, the Cl0p ransomware group has taken credit for the GoAnywhere attack, telling Bleeping Computer that they managed to steal data from more than 130 organizations. However, the hackers have not provided any evidence to back their claims. At the time of writing, there is no mention of Fortra or GoAnywhere on Cl0p’s Tor-based website.
If confirmed, this would not be the first time cybercriminals linked to the Cl0p ransomware have exploited vulnerabilities in a file transfer service used by major organizations to steal data.
In late 2020, a group targeted Accellion’s FTA service to steal data belonging to several organizations, including grocery and pharmacy chain Kroger, the Australian Securities and Investments Commission (ASIC), law firm Jones Day, the Office of the Washington State Auditor (SAO), and the Reserve Bank of New Zealand.
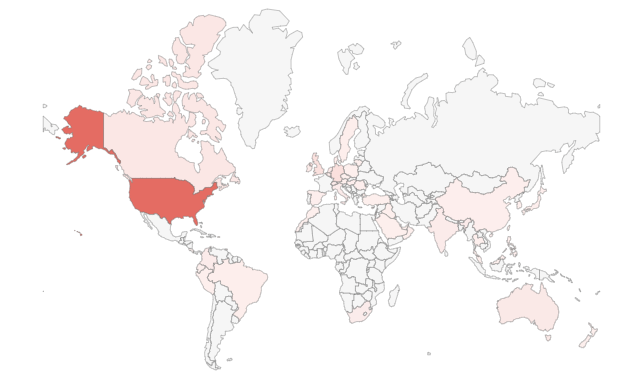
At the time of writing, there are more than 1,000 internet-exposed instances of GoAnywhere. However, according to Fortra, exploitation requires access to the application’s admin console, and at least some of the exposed instances are associated with the product’s web client interface, which is not impacted.
CISA has added CVE-2023-0669 to its Known Exploited Vulnerabilities Catalog, instructing federal agencies to patch the flaw until March 3.
Related: Patch Tuesday: Microsoft Plugs Windows Hole Exploited in Ransomware Attacks
Related: Decade-Old Adobe ColdFusion Vulnerabilities Exploited by Ransomware Gang
Related: PetitPotam Vulnerability Exploited in Ransomware Attacks













