Git repository hosting service GitHub has doubled the maximum amount of money it’s prepared to pay out to researchers who responsibly disclose vulnerabilities.
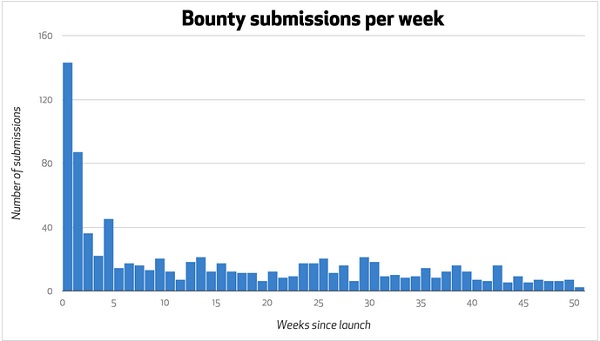
GitHub launched its bug bounty program exactly one year ago. Over the past year, security experts submitted a total of 1,920 reports, of which 869 warranted further review. In the end, 73 previously unknown vulnerabilities were fixed, the company said.
As far as rewards are concerned, GitHub has paid out a total of $55,100 to 33 researchers who reported 57 medium to high risk security flaws. Up until this week, the maximum bounty payout was $5,000, but now GitHub has decided to double it to $10,000.
The top reporters so far are Aleksandr Dobkin, joernchen of Phenoelit, and Russian software developer Egor Homakov.
Dobkin has reported remote code execution, arbitrary file read, stored cross-site scripting (XSS), open redirect, and other types of vulnerabilities. One of the most interesting bugs identified by the researcher is a DOM-based XSS that leveraged a previously unknown flaw in Chrome. The vulnerability could have been exploited to bypass GitHub’s Content Security Policy.
Joernchen has discovered a MySQL typecasting authentication bypass, a two-factor authentication brute force issue, and a bug that could be leveraged to view the members of a team without authorization. However, the most interesting issue reported by the researcher is a vulnerability that could have been used to set arbitrary environment variables. The expert demonstrated that an attacker could have even executed arbitrary commands by exploiting this flaw.
GitHub’s bug bounty program covers the GitHub API, Gist, GitHub.com, and other applications developed and maintained by the company.
Bug bounty programs are said to be more cost-effective than hiring a team of security experts. This is probably why several high-profile organizations have launched responsible vulnerability disclosure programs over the past year. The list includes Twitter, Pinterest, Blackphone/Silent Circle, and Riot Games.














