Open source components have been increasingly used by developers, but failure to patch vulnerabilities in this type of software can pose serious risks.
The 2018 Open Source Security and Risk Analysis (OSSRA) report published on Tuesday by Synopsys shows that of the more than 1,100 commercial codebases analyzed by the company last year, 96% contained open source components, the same percentage as the previous year. However, many applications now contain more open source than proprietary code, with the percentage of open source components in the codebases of scanned apps increasing from 36% in 2016 to 57% in 2017.
The study shows that 78% of the examined codebases were plagued by at least one open source vulnerability, compared to 67% in the previous year. The average number of flaws discovered per codebase in 2017 was 64, which represents an increase of 134%.
Synopsys noted that more than 4,800 vulnerabilities were found in open source software last year, which is not surprising considering that the total number of flaws recorded by the National Vulnerability Database (NVD) exceeded 14,700, compared to only 6,400 in 2016.
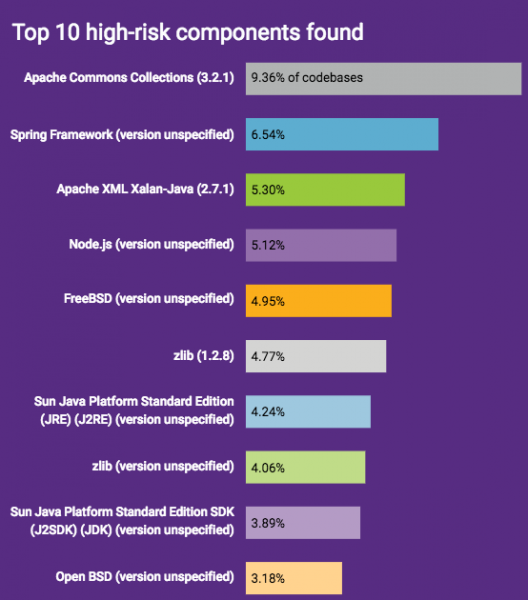
More than half of the vulnerabilities identified during Synopsys’ analysis have been classified as “high risk” and 17% of them have been highly publicized (e.g. Heartbleed, Logjam, FREAK, DROWN, POODLE). Logjam was the most common, being found in 11% of codebases.
Another highly publicized security hole, the Apache Struts 2 flaw exploited in the massive Equifax hack (CVE-2017-5638), was found in 33% of the codebases that used Struts.
The study is based on data collected from a wide range of sectors, including cyber security, automotive, big data, financial services, enterprise software, healthcare, manufacturing, mobile app markets, and Internet of Things (IoT). The largest percentage of high risk open source flaws was identified in the applications of Internet and software infrastructure (67%), Internet and mobile apps (60%), virtual reality, gaming and media (50%), and cybersecurity companies (41%).
The report from Synopsys also highlights another – often overlooked – major risk associated with open source software, namely license issues.
“Open source components are governed by one of about 2,500 known open source licenses, many with obligations and varying levels of restriction. Failure to comply with open source licenses can put businesses at significant risk of litigation and compromise of IP,” the company said in its report. “These license requirements can be managed and complied with only if the open source components governed by those licenses are identified. Just as with security vulnerabilities, it is impossible to manage license compliance risk if the components used aren’t identified.”
Related: Slack Releases Open Source Secure Development Lifecycle Tool
Related: HackerOne Offers Free Service to Open Source Projects













