South Korean carmaker Hyundai has released updates for its Blue Link mobile applications to address vulnerabilities that could have been exploited by hackers to locate, unlock and start vehicles.
The Blue Link application, available for both iOS and Android devices, allows users to remotely access and monitor their car. The list of features provided by the app includes remote engine start, cabin temperature control, stolen vehicle recovery, remote locking and unlocking, vehicle health reports, and automatic collision notifications.
Researchers at security firm Rapid7 discovered that the app had two potentially serious flaws related to a log transmission feature introduced in December 2016.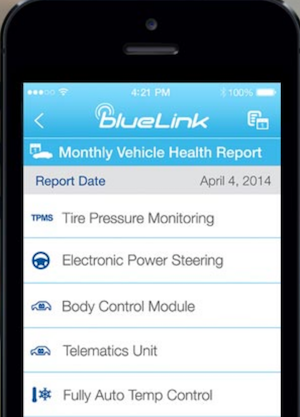
Versions 3.9.4 and 3.9.5 of the Blue Link apps upload an encrypted log file to a pre-defined IP address over HTTP. The name of the file includes the user’s email address and the file itself contains various pieces of information, such as username, password, PIN, and historical GPS data.
While the log file is encrypted, the encryption relies on a hardcoded key that cannot be modified. A man-in-the-middle (MitM) attacker — e.g. via a compromised or rogue Wi-Fi network — can intercept HTTP traffic associated with the Blue Link application and access the log file and the data it contains.
The information in this log file can be used by the attacker to locate, unlock and start the targeted vehicle.
Rapid7 has published a blog post detailing the vulnerabilities. ICS-CERT has also released an advisory which rates the MitM issue (CVE-2017-6052) as a medium severity flaw and the hardcoded cryptographic key weakness (CVE-2017-6054) as high severity.
The flaws were discovered by Rapid7 in February and Hyundai patched them in March with the release of Blue Link 3.9.6 for both iOS and Android. The new version removes the log transmission feature and disables the TCP service located at the IP address where the log files were sent. Hyundai has made the app update mandatory for users.
Hyundai said there was no evidence that the vulnerabilities had been exploited for malicious purposes.
While the flaws could have had a serious impact, Rapid7 and Hyundai pointed out that it would have been “difficult to impossible to conduct this attack at scale,” due to the fact that the attacker needed privileged network access in order to exploit the security holes.
The fact that a mobile application provided by a car manufacturer is vulnerable to hacker attacks is not surprising. In the past months, researchers reported finding flaws in many car apps, including from Tesla.
Related: Flaws in Bosch Car Dongle Allow Hackers to Stop Engine
Related: FBI Reminds That Cars are Increasingly Vulnerable to Remote Exploits













