Companies are increasingly moving sensitive data to the cloud, but cybersecurity, including the human factor and technology, is still a problem for many, according to a new report published on Wednesday by Oracle and KPMG.
The 2019 Cloud Threat Report is based on a survey of cybersecurity and IT professionals from over 450 organizations in North America, the UK, Australia and Singapore.
The study shows that 70% of organizations use more business-critical cloud services year-over-year and it is estimated that the number of companies with at least half their data in the cloud will increase 3.5 times from 2018 to 2020. More than 70% of respondents said that a majority of the data stored in the cloud will be sensitive, up from 50% in the previous year.
On the other hand, there is still a significant security gap, and one of the biggest challenges is related to the shared responsibility security model, where both cloud customers and the cloud service provider play a role in securing infrastructure and applications.
The cloud service provider is typically responsible for virtualization, network, infrastructure and physical security, while the user is responsible for data security, identity management and access. The security of applications and guest operating systems can be the responsibility of either the user or the provider, depending on the type of service.
However, the survey shows that roughly half of respondents are confused about their obligations, even individuals who should be the most knowledgeable, such as the CISO and CIO. Oracle says only 10% of CISOs and 25% of CIOs fully understand this security model.
The fact that the shared responsibility model is different based on the type of service provided – either software-as-a-service (SaaS), infrastructure-as-a-service (IaaS) or platform-as-a-service (PaaS) – can make everything even more confusing for cloud users and nearly 90% admit that understanding the differences between these types of services has been a significant challenge.
This confusion has resulted in the introduction of malware (34% of respondents), increased risk of auditing (32%), unauthorized access to data (30%), and unpatched or misconfigured systems getting compromised (29%). Overall, 82% of cloud users say they have experienced a security incident due to confusion, the report shows.
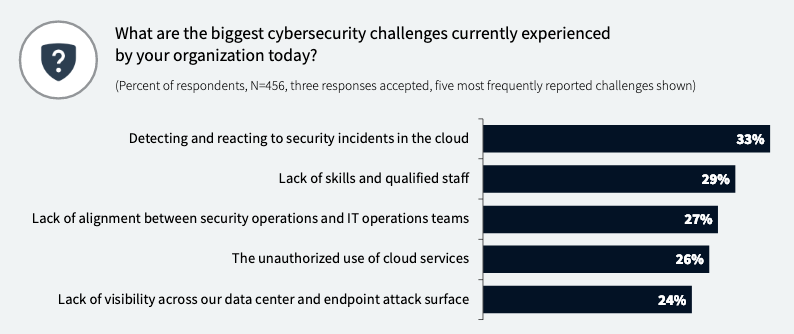
Other significant challenges experienced by organizations include detecting and responding to security incidents in the cloud, lack of skills, lack of alignment between IT and security operations, unauthorized use of cloud services, and lack of visibility.
When it comes to their ability to analyze security event data at scale, only 12% believe they are capable of analyzing over 75% of data, and there is a disconnect between what practitioners say (only 8% believe they have this ability) and what CIOs say (16% reported that their organization can do it). Over 40% of respondents believe they can analyze 40% or less of security event data.
When it comes to patching, many organizations admit that they may delay a patch to a production system if the downtime impacts the ability to meet service level agreements, or if there are software compatibility issues, due to the lack of approval from various teams, or if the risk of exploitation is low. These fears are largely based on incidents that hit the respondents’ organizations in the past two years.
However, patch management plays an important role for most organizations, with 43% saying they have already implemented automated patch management and 46% saying they plan on doing so in the next 1-2 years.














