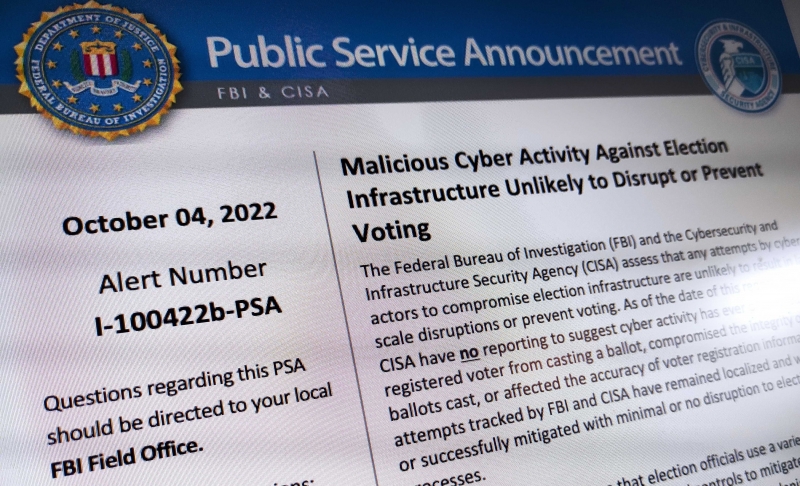
The FBI and CISA have issued a public service announcement (PSA) to say that, based on their assessment, malicious cyber activities are unlikely to significantly disrupt the upcoming midterm elections in the United States.
The agencies have been tracking threat actors’ attempts to compromise election infrastructure, but said these attempts were localized and they were blocked or mitigated with minimal or no disruption. They are confident that threat actors are unlikely to be able to cause any large-scale disruption or prevent people from voting.
“As of the date of this report, the FBI and CISA have no reporting to suggest cyber activity has ever prevented a registered voter from casting a ballot, compromised the integrity of any ballots cast, or affected the accuracy of voter registration information,” the PSA reads.
The FBI and CISA warn that threat actors continue to be interested in election systems hosting voter registration information and ones that manage non-voting election processes. They also spread or amplify false claims of election infrastructure getting compromised.
However, the agencies say these attempts cannot prevent voting or the accurate reporting of election results. In addition, they have assured the public that technological, procedural and physical controls are in place to prevent malicious cyber actors from altering votes or blocking people from voting.
The FBI warned earlier this year that US election officials had been targeted in phishing attacks.
The PSA comes just days after senior FBI officials warned that Russian and Chinese government-affiliated entities are promoting misinformation about the integrity of US elections.
Facebook parent Meta announced in late September that it had removed two unconnected networks traced to China and Russia, which abused its platform to conduct influence operations. The Chinese operation, which ran across multiple social media platforms, was the first to target US domestic politics ahead of the midterms, Meta said.
The Russian operation disrupted by Meta did not target the elections, but the FBI said Russia’s operations are more pronounced compared to the Chinese.
On Wednesday, authorities announced that 51-year-old Eugene Yu, the founder and CEO of election software company Konnech Corporation, has been arrested on suspicion of stealing data on hundreds of poll workers in Los Angeles county.
Konnech, whose software is designed for tracking election worker schedules, training and payroll, was required to keep the data in the US, but instead allegedly stored it on Chinese servers.
Authorities did not specify what information may have been compromised, but noted that it only involved poll workers, not voting machines or vote counts.
Konnech and Chinese-born Yu were accused by election conspiracy theorists of having ties to the Chinese Communist Party and supplying them with information on millions of poll workers.
Related: Election Officials Face Security Challenges Before Midterms
Related: Attacks From Within Seen as a Growing Threat to Elections















