NASA’s Orion spacecraft was launched today, and it’s possible that the microchip containing the names of the 1.3 million individuals who got a boarding pass for the test flight also stores a payload injected by researchers at Germany-based Vulnerability Lab.
In October, NASA launched a special website where users could get a boarding pass to fly their name on Orion’s first flight. However, researchers discovered that the fields where users entered their first name and their last name were plagued by a persistent input validation Web vulnerability.
“A filter bypass and persistent input validation web vulnerability (embed code execution) has been discovered in the official NASA Mars Program web-application,” Vulnerability Lab wrote in an advisory. “The high severity vulnerability allows remote attackers to inject own system specific codes to the application-side of the affected NASA online-service website.”
Benjamin Kunz Mejri, the founder of Vulnerability Lab, said he reported the vulnerability to NASA on October 10 through the United States Computer Emergency Readiness Team (US-CERT), but not before injecting three payloads to test the flaw.
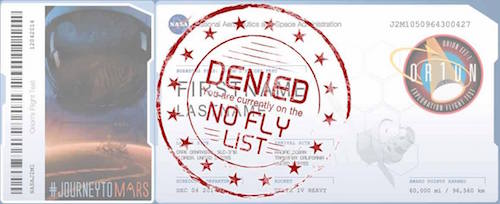
NASA addressed the issue in mid-November and put Kunz Mejri’s name on a “No Fly List”, but the expert believes the agency spotted only two of the payloads, while one passed the verification process.
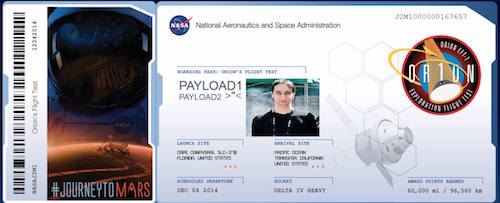
The space agency said all entries were exported and reviewed by a team of people so it’s unlikely that unauthorized data made it through, but the researcher argues that they couldn’t have checked all 1.3 million entries. Kunz Mejri found that one of his test payloads was still marked as a valid ticket for the Orion flight scheduled for December 4.
Even if the payload made it onto the microchip, NASA says there are no risks.
“Approved names were then converted into a form for putting on the chip through e-beam lithography – not only is there no issue of corrupting the chip, but there is no computer-based or other use of the chip so there is no risk in any case,” NASA representatives told SecurityWeek.














