A cyber-espionage campaign at the center of recent reports about attacks targeting Israel has been underway for the past year, according to security vendor Norman ASA.
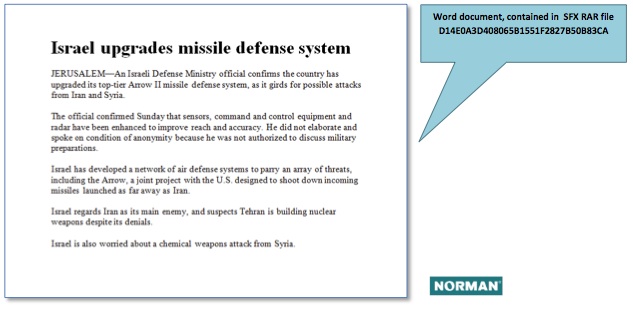
The discovery follows revelations publicized in late October that resulted in Israel shutting down Internet access for its police force and banning them from using USB sticks or disks in order to stem a cyber attack that was uncovered when a malicious email was found disguised as a message from Benny Gantz, chief of general staff of the Israel Defense Force (IDF). Hidden with the email was a piece of malware known as Xtreme RAT, a remote access Trojan that can be used to steal system information.
According to Trend Micro, the latest version of the Trojan includes Windows 8 compatibility and enhanced desktop and audio capture capabilities. In addition to this latest attack campaign, Xtreme RAT has also been seen in previous attacks targeting Syrian anti-government activists.
Snorre Fagerland, principal security researcher at Norman, said in a blog post that the malware was signed with a fake digital certificate. The certificate chain ends in an untrusted root certificate and therefore would not be validated. After searching the company’s databases for the faked certificate, it was discovered that several other Trojans similarly signed, and then many more Trojans that connected to the same command and control structure. The C&C structure, he explained, is centered around a few dynamic DNS domains that point to hosting services in the U.S.
The older files uncovered by the company used bait documents and videos written in Arabic that were aimed primarily at a Palestinian audience, while the newer files were targeted more towards Israelis, Fagerland noted. The older files go back to October 2011. Though they “more or less” use the same C&C infrastructure, the C&C host names resolved to IP addresses in Palestine at the time, he explained.
“The bait files seem to focus on a number of areas (military, political and religious) which hints at a broad targeting, not only a specific sector,” Fagerland told SecurityWeek.
“The malware is off-the-shelf, cheap stuff. No zero-days were seen, though there are a few tricks used; such as using special Unicode characters to reverse text direction, and thus hide the executable file extension,” he said.
Norman’s full 25-page report on the attack campaign can be found here in PDF format.














