Researchers at ESET have discovered a targeted cyber espionage campaign in Pakistan, which is attempting to compromise sensitive information from various organizations. While limited, traces of the same attack have also been discovered in other parts of the globe.
The attack targets a vulnerability in Microsoft Office, CVE-2012-0158, which if exploited, allows the attacker to install malicious software up to and including backdoors.
Last year, when criminals focused on this vulnerability at its peak, the Web was flooded with malicious documents. Other attack vectors include the use of malicious PDF files that first send system information to a remote site, before downloading additional malware onto the system.
There’s also evidence that the attackers are signing their code with an old certificate that was issued in 2011 to Technical and Commercial Consulting Pvt. Ltd., a firm based in New Delhi, India.
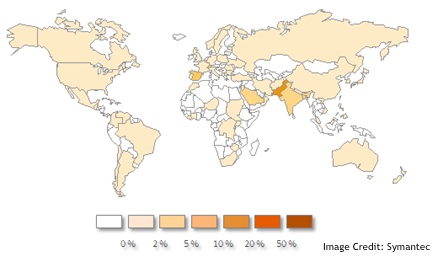
According to ESET, 80% of the attack has focused on Pakistan, though traces of it have also been noted in the U.S., the Ukraine, China, Russia, Spain, and India.
According to Symantec, the attack appears to be no more than four years old and very broad in scope, but appears to be focused on government agencies located in Pakistan.
Telemetry data focused on South Asia (Symantec)
“We have identified several different documents that followed different themes likely to be enticing to the recipients. One of these is the Indian armed forces. We do not have precise information as to which individuals or organizations were really specifically targeted by these files, but based on our investigations, it is our assumption that people and institutions in Pakistan were targeted,” said Jean-Ian Boutin, a malware researcher at ESET.
The payloads dropped by the malware offer a range from access. ESET discovered downloaders, document uploaders, keyloggers, reverse shells, and payloads with the ability to self-replicate within a network. Further, they also found two public tools (WebPassView and Mail PassView from NirSoft) signed by the malicious certificate.
Once compromised, the malware starts harvesting data immediately, but sends it to the attacker’s systems unencrypted.
“The decision not to use encryption is puzzling considering that adding basic encryption would be easy and provide additional stealth to the operation,” said Boutin.
While unrelated, researchers from Trustwave found the same vulnerability being exploited by Cutwail botnet over the past week, which has been sending out spam containing malicious documents that target CVE-2012-0158. “The use of a loaded RTF attachment is a departure from normal for Cutwail, usually it distributes executable attachments or links to exploit kits,” Trustwave’s Rodel Mendrez noted in a blog post. Mendrez also pointed out that the same vulnerability had been used in targeted attacks against NGOs and human rights activists in 2012.
Additional technical details from ESET on the attacks targeting Pakistan are online.
Additional reporting by Mike Lennon















