There has been no shortage of news recently about North Korea and how the hermit nation controls the Internet usage of its citizens. Security researcher Robert Hansen, VP of WhiteHat Labs at WhiteHat Security, recently dug into the software used by North Koreans and discovered the extent that the government goes to censor and monitor all Internet activity within its borders.
“It’s weirder than we thought,” Hansen said.
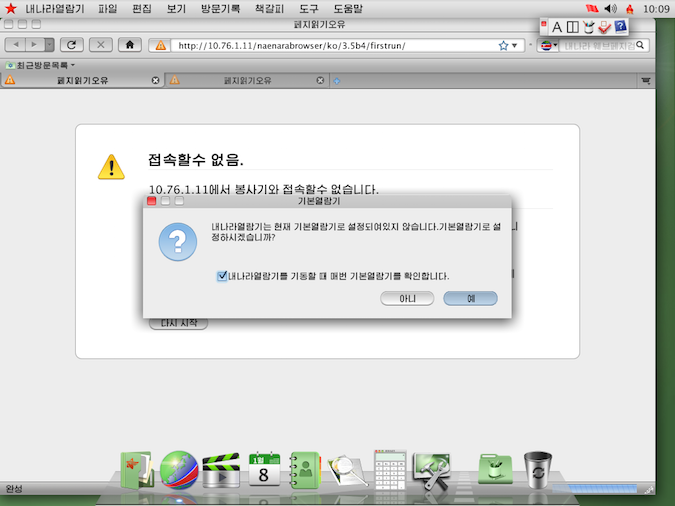
Hansen was digging into the Naenara Browser, a version of Mozilla Firefox modified by North Korea and bundled into Red Star OS, the country’s official operating system. Red Star OS restricts what reaches the browser and network, allowing the government limit what their people get to do, see, and contribute, Robert Hansen, vice-president of White Labs at White Hat Security, wrote in a blog post Thursday.
When the Naenara Browser is first run, it immediately makes a request to another IP address, Hansen found. That in itself was not remarkable, except for the fact that the address it called was not a public address, but rather, one meant for internal networks. Addresses in the 10.x.x.x space are not designed to be routable on the Internet, but it appears from Hansen’s explorations that all of Democratic People’s Republic of Korea (DPRK) is non-routable IP space. It was well known that North Korea exercised rigid control over what IP addresses were used because it owned a small block of IP addresses, but it appears to be funneling all traffic through one—or a handful—of public IP addresses.
“They’re treating their entire country like some small to medium business might threat their corporate office,” Hansen wrote.
The configuration settings in Naenara 3.5, which felt like Mozilla “a half dozen major revisions out of date,” revealed more information about how the government monitors Internet activity. The browser uses the same tracking systems used in Google’s Safe Browsing API but created their own unique keys, Hansen said. The system allowed Google to push down updates and anti-phishing blacklists; presumably Naenara uses the system for its own software updates. Hansen noted the mechanism could be used to identify users as they moved across the network.
While Hansen suggested Google intentionally built in the ability to decloak users into this system, several commenters on a Hacker News thread noted the unique user keys were necessary to get updated before Google had switched over all its sites to HTTPS.
It appeared the “mothership”—the IP address Naenara browsers immediately connect to when launched—acted as a proxy server for the entire country, Hansen said. All email also appears to pass through the same address, which makes the system vulnerable to man-in-the-middle attacks and sniffing. User calendars are also exposed, making Hansen wonder why HTTPS wasn’t rolled out internally.
“But I guess no one in DPRK has any secrets, or at least not over email,” Hansen wrote.
Hacker News commenter “Pilif” noted that the government doesn’t care if “normal” people could potentially sniff each other calendars. “If the government wants access to the calendar, they just look the data up I guess and because this is all a big intranet, the traffic doesn’t cross any non-goverment-owned routers anyways,” Pilif wrote.
Naenara also accepts only North Korean-signed certificates. That is no surprise, considering how strict the government censorship is in this small country. This makes man-in-the-middle attacks on any outbound HTTPS connection “trivial,” and also prevents other governments from man-in-the-middle attack North Korean users. WikiLeaks documents showed otherwise, but it showed how the North Korean government had to “rely on draconian Internet breaking concepts like this,” Hansen noted.
Snort intrusion detection system is installed by default in Red Star OS, so it would be easy for government officials to check a user’s computer and easily find everything that had been done. “Using your neighbor’s Wi-Fi isn’t a safe alternative for a political dissident using Red Star OS,” Hansen said.
Hansen felt it was “odd” that the entire country could run off one IP address. “Ultimately running anything off of one IP address for a whole country is bad for many reasons,” he said.
It seems pretty reasonable when considering the small portion of population who has access to the Internet in the first place—when the total number of Internet users number in the thousands, it’s convenient to run it through this system. And as the same Hacker News thread noted, Red Star OS is not the only system being used in North Korea, and researchers and students at universities are given access to the broader Internet.
North Korea goes to great lengths to limit what their people can do. “It’s quite a feat of engineering. Creepy and cool,” Hansen said.














