Cyber criminals rarely waste time when it comes to taking advantage of news items that could be used for attacks. The recent launch of Microsoft’s Windows 8 operating system is no exception.
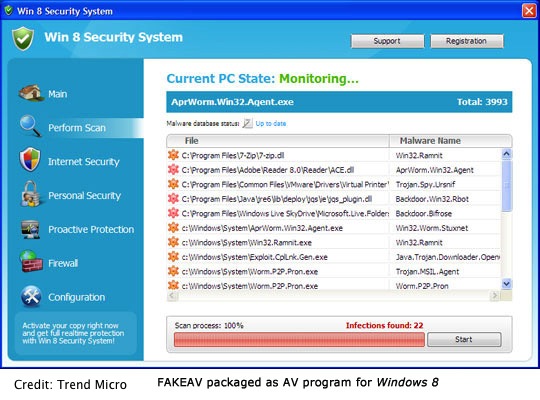
According to Trend Micro, attackers have begun trying to rope users in with promises of antivirus. The malware, which the firm detects as TROJ_FAKEAV.EHM, follows the footsteps of a typical fake antivirus scheme by displaying a bogus scanning result to trick the user into purchasing the phony program. The only difference is this malware is packaged to look like a security program made for Windows 8, blogged Gelo Abendan of Trend Micro.
A second scheme utilizing the news of Windows 8 involves a phishing email designed to lure users to a website where they can download the operating system for free. Instead of the OS however, users are taken to a phishing site that asks for personally information, including email addresses, passwords and names that can be sold in the underground market.
“It is typical for cybercriminals to piggyback on the highly-anticipated release of any latest technology to take their malware, spam, malicious app to new heights,” noted Abendan. “The appearance of the Instagram app we previously reported coincided with the news of Facebook’s acquisition of the photo sharing app. Similarly, malicious versions of Bad Piggies surfaced right after the app’s launch.”
“To stay safe, users must keep their cool and think twice before clicking links or visiting webpages, especially those that promise the latest items or programs for free,” Abendan added.
















