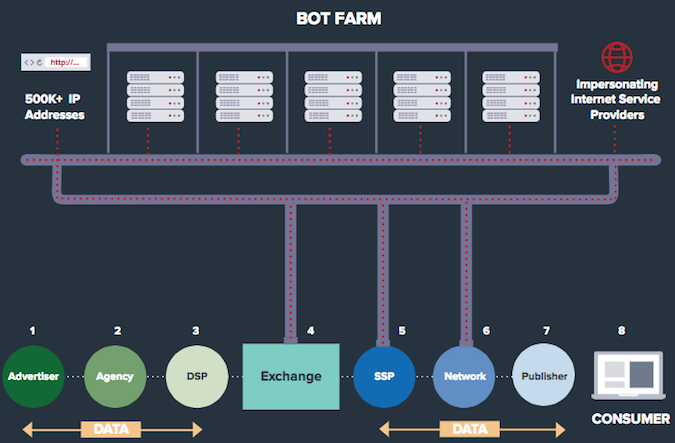
Russian cybercriminals can earn up to $5 million per day through a massive ad fraud operation powered by a bot farm that uses hundreds of servers and more than 500,000 IP addresses, online fraud detection firm White Ops reported on Tuesday.
Ad fraud typically involves malware-infected computers that cybercriminals abuse to generate fake advertising traffic. However, in the campaign observed by White Ops over the past three months, dubbed Methbot, the scammers created their own “users.”
The cybercrooks rely on 800-1,200 servers housed by data centers located in Dallas and Amsterdam, and more than 570,000 IPv4 addresses made to look as if they belong to residential ISPs in the United States. The value of these IP addresses has been estimated at more than $4 million.
Methbot uses Node.js and various open source libraries to simulate a web browser. In order to avoid being flagged by bot detection systems, it spoofs user agent strings for various browsers and operating systems, including Chrome, Firefox, Internet Explorer, Windows and Mac OS X.
Furthermore, the bot farm is capable of emulating browser windows, mouse cursor movements, clicks and even social media logins in an effort to convince advertisers that the traffic is generated by real people.
In the first phase of the operation, Methbot selects a domain or a URL from a list of premium publishers. A fake webpage that contains only the elements needed to support an ad is generated and a video advertisement is requested from an ad network using a spoofed URL matching the one of the publisher. The ad is loaded in the simulated browser through a proxy and the various human-mimicking mechanisms are enabled to trick anti-fraud systems into believing that the activity is the result of real user interaction.
Researchers said the attackers spoofed the domains of more than 6,000 publishers, including companies such as Vogue, The Economist, ESPN, Fortune, Fox News and International Business Times.
By targeting premium video ads and making it appear as if the ad has been accessed from a high-value geographical location, the cybercriminals behind Methbot can earn between $3 million and $5 million per day, White Ops determined after consulting programmatic media intelligence firm AD/FIN. Experts said Methbot generates 200 – 300 million fake impressions every day, with the CPM (cost per thousand impressions) ranging between $3.27 and $36.72.
If these figures are accurate, the financial damage caused by Methbot is far greater than in the case of other botnets, such as ZeroAccess ($900,000 per day), Chameleon ($200,000 per day), and Avalanche ($40,000 per day).
White Ops has shared a list of IP addresses, spoofed domains and URLs used by Methbot in an effort to help advertisers and technology providers block attacks.
Related: Impression Fraud Botnet Could Cost Advertisers Billions















