Researchers discovered that the Control Web Panel (CWP) web hosting panel is affected by two serious vulnerabilities that can allow attackers to remotely hack servers, and it’s possible that they may have already been exploited in the wild.
CWP, which has both free and paid versions, is an advanced Linux control panel designed for web hosting providers and system administrators.
In a blog post published last week, Octagon Networks, which describes itself as a global team of hackers and security researchers, disclosed the details of two vulnerabilities that can be chained to hack servers running CWP, remotely from the internet and without any user interaction.
One of the vulnerabilities is CVE-2021-45467, described as a file inclusion issue, and the other is CVE-2021-45466, a file write flaw. Chaining the two security holes can lead to unauthenticated remote command execution with root privileges.
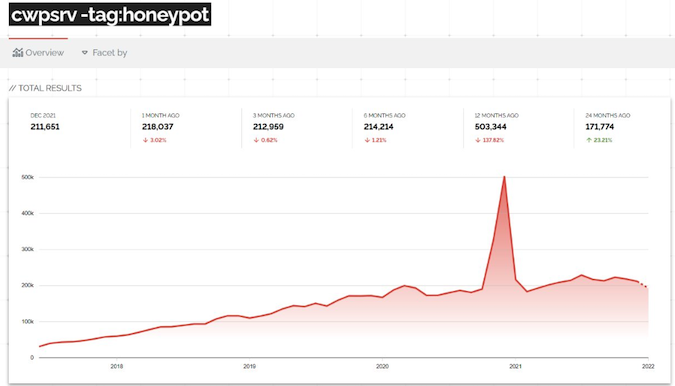
While the developer of CWP says on its website that there are 30,000 servers running the control panel, Octagon researchers noted that the Shodan and Censys internet search engines show over 100,000 results each.

Shodan told SecurityWeek that there has been a steady increase in the use of CWP over the past years.
According to the blog post published by Octagon, they have seen indications that someone has managed to “reverse the patch and exploit some servers.”
Octagon’s Paulos Yibelo told SecurityWeek that while they are not sure whether the vulnerabilities have in fact been exploited, it is “possible.”
CWP developers patched the vulnerabilities with recent updates.
In addition to the blog post describing the findings, Octagon has released a video showing the exploit in action, and they also plan on making public a full proof-of-concept (PoC) exploit after admins have had enough time to install the patches.
*updated with information from Shodan
Related: High-Risk Flaw Haunts Apache Server
Related: Recently Patched Apache HTTP Server Vulnerability Exploited in Attacks














