A report published by Kaspersky Lab on Thursday shows that the number of attacks involving exploits increased significantly in 2016 compared to the previous year, but the number of attacked users actually dropped.
The security firm observed more than 700 million attempts to execute an exploit in 2016, which represents a 25% increase compared to 2015. However, the number of users attacked was only 4.3 million, compared to nearly 5.5 million in the previous year.
This indicates that while fewer users encountered exploits, the likelihood of coming across an exploit increased as the number of websites and spam messages delivering such threats has continued to grow.
Of all the exploit attacks observed by Kaspersky in 2016, more than 15% were aimed at corporate machines. The number of targeted corporate users increased from 538,000 in 2015 to 690,000 in 2016.
While Windows and web browsers were the most targeted applications in both 2015 and 2016, their share decreased significantly last year, making more room for Android and Microsoft Office exploits.
“Exploits for vulnerabilities in Office software became the absolute champions in terms of the number of attacked users. They increased by almost 103% to reach 367,167 attacked users,” Kaspersky said in its report.
The security firm said more than 297,000 users were hit by zero-day or heavily obfuscated known exploits in 2016, and the most common exploit, same as in the previous year, was CVE-2010-2568, a vulnerability leveraged by the notorious Stuxnet malware.
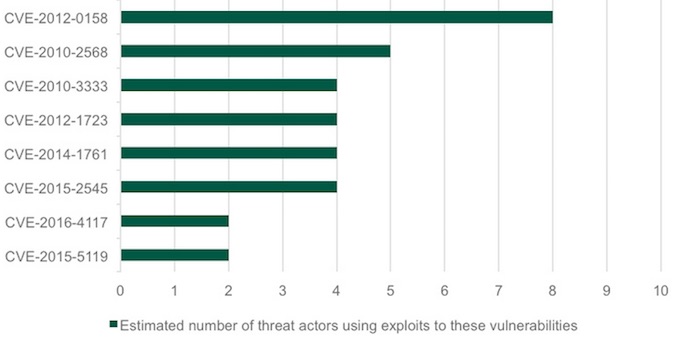
Between 2010 and 2016, malicious actors used more than 80 vulnerabilities in targeted attacks. The Russia-linked threat group known as APT28 and Fancy Bear leveraged 25 flaws, including at least six zero-days, followed by the NSA-linked Equation Group, which used roughly 17 vulnerabilities, including at least eight zero-days.
Groups that launched targeted attacks have mainly relied on Windows flaws, followed by Flash Player, Office, Java and Internet Explorer. The most popular vulnerability is CVE-2012-0158, which is still being used by APT actors.
Related: Exploit Kits Take Cyberattacks to the Masses, But They’re Preventable
Related: New Terror Exploit Kit Emerges













