Citadel Variant Adds Automatic Language Localization To Target International Markets
Researchers at Trusteer have discovered a new variant of the Citadel Trojan that includes HTML injections that focus on specific domains, including those in social media, banking, and e-commerce.
The crew behind this latest build have taken their time to develop a versatile payload that brings a higher level of customization than has been used in the past for this malware. According to Trusteer, the gang behind this latest variant has developed regional-based injects that match language.
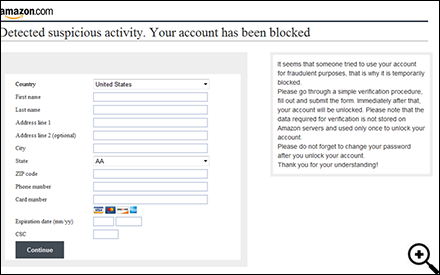
The malware includes injects localized in Italian, Spanish, French, German, and English, which in itself is split into American, Canadian, British, and Australian. Each inject will focus on a specific domain, the most notable being Amazon. In a blog post, Trusteer posted a screenshot of the Amazon inject, which asks for personal and financial data in order to overcome an alleged security check.
Trusteer highlighted the following example for a heading targeting Amazon customers: “Detected suspicious activity. Your account has been blocked”. Depending on what international Amazon site a user may be visiting, the malware is set to change the language accordingly:
• Amazon.fr – “On dtecte l’activitmfiante. Votre compte est bloqu”
• Amazon.de – “Es wurde die verdchtige Aktivitt bemerkt. Ihr Account wurde gesperrt”
• Amazon.it – “Si e’ verificata un attivita’ sospetta. Il Suo account e’ stato bloccato.o”
• Amazon.es – “Se ha detectado actividad maliciosa. Su cuenta ha sido bloqueada”
“The sophistication of the malware combined with the low profile maintained by the criminal gang suggests that this is the work of a highly sophisticated cybercrime team,” Trusteer’s post explains.
“The use of a single variant that is capable of targeting multiple international brands provides a significant advantage in the monetizing process that follows. The malware not only collects login credentials, it also captures credit card data that can be sold separately to other criminals.”
The regional focus makes it easier to sell the harvested credentials. For example Spanish criminals will likely find it easier to cash-out Spanish accounts rather than American ones, and they’re likely to sell access to clients on a regional level. Aside from Amazon, Trusteer didn’t mention any other e-commerce or financial targets in the latest Citadel build, but given that it’s modular – it can be customized to target just about anything.
The fact that this new variant of the Citadel Trojan has started to spread online isn’t shocking in the least, and its not the end of the world, but it is likely to be more effective for attackers.
Earlier this month, Microsoft, along with other financial services organizations, and law enforcement, announced the successfully shutdown of more than 1,000 botnets that utilized the Citadel malware. The botnets combined were responsible for over half a billion dollars in financial fraud and affected more than five million people in over 90 ninety countries, Microsoft said.
Additional details are available on Trusteer’s blog.
Additional reporting by Mike Lennon
















