Tens of millions of Cisco devices deployed in enterprise environments are exposed to attacks due to vulnerabilities identified by researchers in a proprietary discovery protocol they all use.
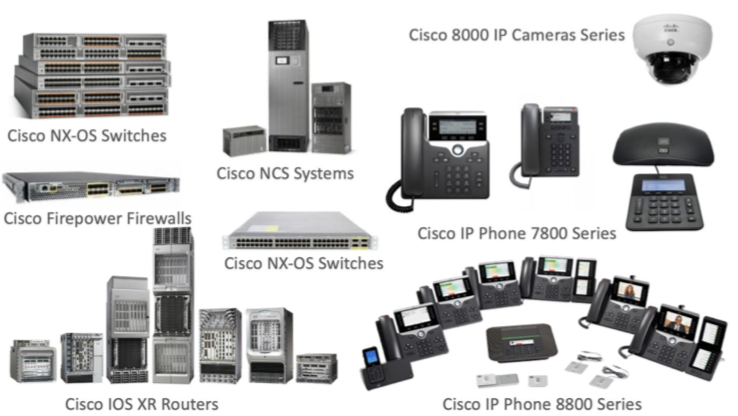
The problematic protocol is the Cisco Discovery Protocol (CDP), a Layer 2 network protocol used to obtain information about Cisco devices present on the local network. The protocol is used by Cisco switches, IP phones, routers and cameras.
Researchers at IoT security firm Armis discovered a total of five potentially serious vulnerabilities in various implementations of the protocol. Some of these flaws, collectively tracked as CDPwn, can be exploited to take complete control of affected devices.
Researchers discovered four remote code execution vulnerabilities — each impacts a different implementation of the CDP parsing mechanism — and one denial-of-service (DoS) vulnerability. The code execution flaws impact the NX-OS, IOS XR, IP phone, and IP camera implementations, while the DoS issue affects the FXOS, IOS XR and NX-OS implementations of CDP.
In order to exploit the weaknesses, an attacker who has gained access to the network needs to send specially crafted CDP packets to the targeted device.
By targeting switches, for example, an attacker could move from one network segment that houses a device compromised in the first phase of the attack to another network segment that may host more valuable information.
Moreover, Armis says, compromising a switch using a CDPwn attack can allow hackers to intercept network traffic and launch man-in-the-middle (MitM) attacks.
“Additionally, a switch is the ultimate hiding position for an attacker – it is an relatively unsecured device, that doesn’t allow any security agent on it, and an attacker has the ability to launch attacks from it to the devices in the network. An attacker could also hide the malicious traffic he generated from any other network taps that are there to inspect traffic,” Armis explained in its report on CDPwn.
Hackers can also exploit the vulnerabilities against IP phones and cameras to exfiltrate potentially sensitive data from such devices. According to Armis, since IP phones are affected by a flaw that is unique to these types of systems, an attacker can broadcast specially crafted exploit packets over the network and target all impacted IP phones at once.
Cisco has released advisories and patches for these vulnerabilities, to which the following CVE identifiers have been assigned CVE-2020-3120, CVE-2020-3119, CVE-2020-3118, CVE-2020-3111 and CVE-2020-3110. The networking giant, which assigned a high severity rating to the flaws, has pointed out that an attacker must be in the same broadcast domain as the affected device.
Related: Cisco Webex Vulnerability Exploited to Join Meetings Without a Password
Related: Cisco Patches DoS, Information Disclosure Flaws in Small Business Switches
Related: PoC Exploits Released for Cisco DCNM Vulnerabilities














